Table of Contents
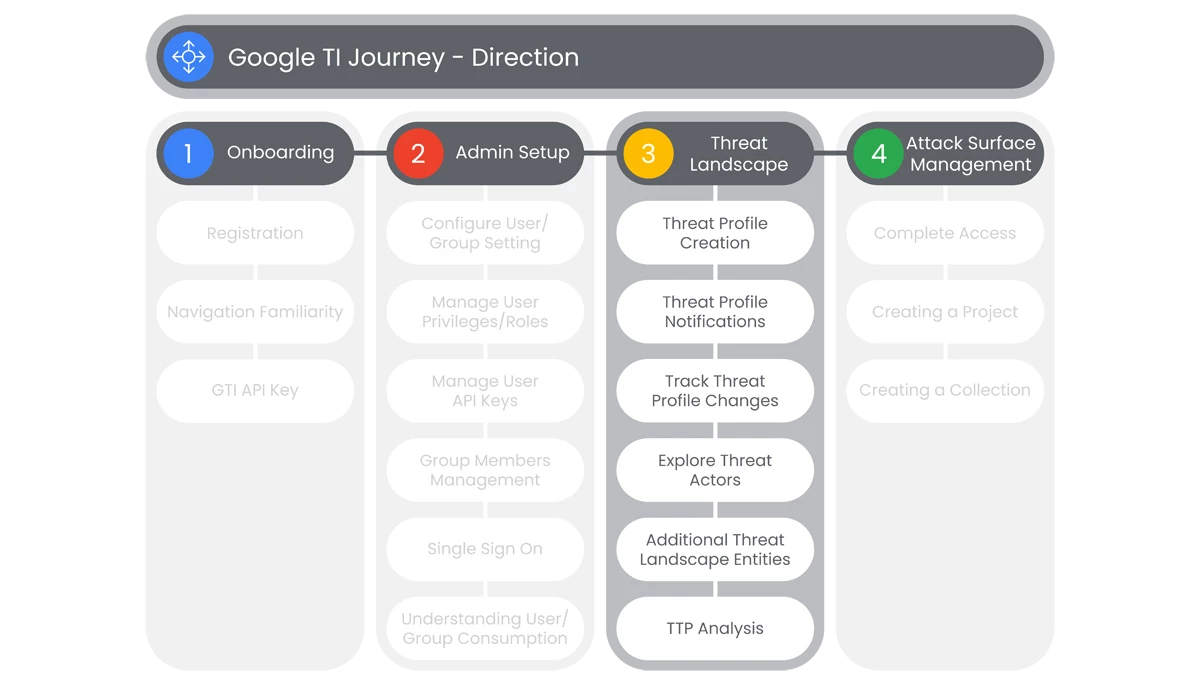
This section of Google Threat Intelligence Onboarding is going to cover the administration of Google TI’s Threat Landscape functionality. Here users will be able to see how to create threat profiles, receive notifications via email, and track updates to threat profiles that the organization is tracking.
Prerequisites
Access to the Homepage and its features, requires the user to have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Actions
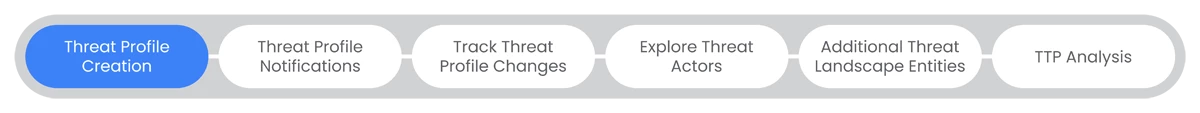
Threat Profile Creation
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles and apply top-level filters for target Industries and target Regions. This assists organizations in identifying and defining threat that are relevant to the organization.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
- On the main page of Google Threat Intelligence Platform, go to the Left Navbar to select Threat Landscape.
- In the dropdown menu, select My Threat Profiles.
- For first time users, there will be sections to enter information, or autofill selections in a dropdown list from existing Projects.
- If users have not created any Threat Profiles, users will see an Introducing Threat Profiles splash page. This page will show a preview of the Threat Profiles page under a link titled “Show Preview.”
- In the middle of the page, users will see a display of two icons:
- View All Profiles
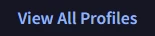
- Create Threat Profile

- View All Profiles
- Users will select Create Threat Profile and a Create Your Threat Profile will appear.
- In the first section, named Create your Threat Profile, users can name a threat profile under the entry box titled Name.
- Click the Next button.
- The next section is titled Choose your area of focus, users can Select an Industry or Select a Target Region, to compile their personalized threat profile view.
- Select Save Threat Profile.
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/threat-profiles#create-a-threat-profile
- Additional Documentation: https://gtidocs.virustotal.com/docs/threat-profiles#create-additional-threat-profiles
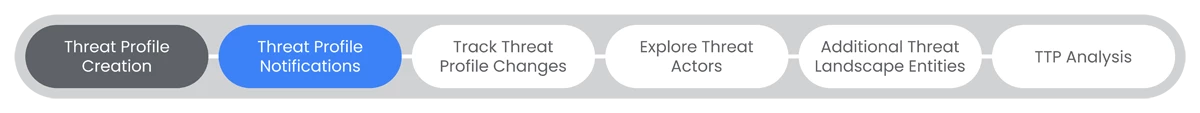
Threat Profile Notifications
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles. Users build a personalized Threat Landscape by creating customizable Threat Profiles from all of Google TI's threat intelligence so you can focus only on the threats that matter most to your organization.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Steps
- To track Threat Profile changes, users will go back to the Left Navbar to select Threat Landscape.
- In the dropdown menu, select My Threat Profiles.
- Select an existing Threat Profile, users will see a page titled Your Threat Profile, that will have multiple categories to select from, dependent on the type of Threat Profile:
- Actors
- Campaigns
- Malware
- Vulnerabilities
- Collections
- Reports
- Below those categories, users will see two tabs:
- Overview
- MITRE ATT&CK
- Below the Overview and MITRE ATT&CK tabs is a dropdown menu for:
- Recommended
- Added
- If users select Recommended in the Overview section, users will be able to see three sections:
- Your Threat Map
- What’s Changed
- Your Recommended Actors
- In the Your Recommended Actors section, users will have download options to either download a .csv file of:
- Indicators
- MITRE TTPs
- Those options can be accessed from the Download button or Take Action button in the Your Recommended Actors section.
- Users who select the MITRE ATT&CK tab of the Your Threat Profile section, users will be able to see a display of the associated MITRE ATT&CK TTPs to the Threat Profile.
- At the top right of the page, users will have the option to download a .csv of the associated TTPs.
- If users select Added in the Overview section, users will be able to see two sections:
- Your Added Actors
- What’s Changed
- Users can Manage Threat Profiles, by going to the top right of the Your Threat Profile page, and clicking on the Profile Switcher.

- Users can select the Create Threat Profile button as another method to create a Threat Profile.

- To manage a Threat Profile, users can select the Manage Threat Profile button.

- The Manage Threat Profile page will appear, where users can select a Threat Profile and choose to:
- Customize Threat Profile
- Copy Threat Profile
- Delete Threat Profile
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/threat-profiles#manage-threat-profiles
- Additional Documentation:
https://gtidocs.virustotal.com/docs/threat-profiles#explore-your-threat-landscape
https://gtidocs.virustotal.com/docs/threat-profiles#create-additional-threat-profiles
Track Threat Profile Changes
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles. Users can track changes to objects in their Threat Profiles. Any changes are tracked and identified for users to stay up to date.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Steps
- To track Threat Profile changes, users will go back to the Left Navbar to select Threat Landscape.
- In the dropdown menu, select My Threat Profiles.
- Select an existing Threat Profile, users will see a page titled Your Threat Profile, that will have multiple categories to select from, dependent on the type of Threat Profile:
- Actors
- Campaigns
- Malware
- Vulnerabilities
- Collections
- Reports
- Below those categories, users will see two tabs:
- Overview
- MITRE ATT&CK
- In the Overview section, users will be able to see three sections where there will be a section on the right-hand side titled What’s Changed.
- In What’s Changed section, users can see any profiles or events that have had changes, to include a search function.
- To receive email notifications of the changes, users will select an icon for the Setup Email Notifications button.

- This will bring users to the Account Settings page, where they can Add Email Notifications to track any changes.
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/threat-profiles#track-changes-to-objects-in-threat-profile
- Additional Documentation: https://gtidocs.virustotal.com/docs/threat-profiles#subscribe-to-email-notifications
Explore Threat Actors
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles and apply top-level filters for target Industries and target Regions. This assists organizations in identifying and defining threat that are relevant to the organization.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Steps
- On the main page of Google Threat Intelligence Platform, go to the Left Navbar to select Threat Landscape.
- A dropdown menu will appear, where users will select the Threat Actors feature. The Threat Landscape page will appear with entity tabs and three sections:
- Search Query bar
- Filters
- Summary
- To view Threat Landscape entities, users can select from the following:
- Threat Actors
- Malware & Tools
- Campaigns
- IOC Collections
- At the top of the page users can see the Search Query bar. Here users can enter searches by:
- Name
- Owner
- Description
- Tags
- Below the Search Query bar users will see the Filter selection dropdown lists.
- The first Filter is an important selection as it is where users can select the Origin of the Report.
- The first Filter is an important selection as it is where users can select the Origin of the Vulnerability reporting:
- Google Threat Intel
- Google Threat Intelligence Reporting
- Partner
- Peer Threat Intelligence Reporting
- Crowd-sourced
- Open-source (OSINT) Reporting
- Google Threat Intel
- The remaining Filters can allow users to select from a variety of options:
- Industries
- Target Regions
- Source Regions
- Threat Category
- Creation Date
- Lookups Trends
- To the right of Lookups Trends dropdown tab, users will see an Actions tab, but only after selecting a Threat Actor(s) from the list in the Summary section.
- The Actions will consist of:
- Follow New IOCs in Your IOC Stream
- Additionally Send Email Notifications…
- If users select to send email notifications, they will enter an email address or multiple.
- Users will then select to receive One Email per IOC Added.
- Or users will choose Daily Digest to receive a daily email in their inbox with all the new IOCs added to the entity.
- Or users will choose Daily Digest to receive a daily email in their inbox with all the new IOCs added to the entity.
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/curated-threat-actors
- Additional Documentation: https://gtidocs.virustotal.com/docs/community-threat-actors
Additional Threat Landscape Entities
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles and apply top-level filters for target Industries and target Regions. This assists organizations in identifying and defining threat that are relevant to the organization.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Steps
- On the main page of Google Threat Intelligence Platform, go to the Left Navbar to select Threat Landscape.
- The Threat Landscape page will appear with entity tabs and three sections:
- Search Query bar
- Filters
- Summary
- To view other Threat Landscape entities, users can select from the following:
- Threat Actors
- Malware & Tools
- Campaigns
- IOC Collections
- At the top of the page users can see the Search Query bar. Here users can enter searches by:
- Name
- Owner
- Description
- Tags
- Below the Search Query bar users will see the Filter selection dropdown lists.
- The first Filter is an important selection as it is where users can select the Origin of the Report.
- The first tab selection dropdown list is where users can select where the Report is sourced from. Users can select Reports from:
- Google Threat Intel
- Google Threat Intelligence Reporting
- Partner
- Peer Threat Intelligence Reporting
- Crowd-sourced
- Open-source (OSINT) Reporting
- Google Threat Intel
- The remaining Filters can allow users to select from a variety of options:
- Industries
- Target Regions
- Source Regions
- Threat Category
- Creation Date
- Lookups Trends
- The IOC Collections page will have two additional Filters of:
- Collection Type
- Visibility
- Below the Filters is the Summary section, that consists of Summary and Activity information.
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/malware
- Additional Documentation: https://gtidocs.virustotal.com/docs/campaigns
- Additional Documentation: https://gtidocs.virustotal.com/docs/ioc-collections
TTP Analysis
Google Threat Intelligence provides a tailored Threat Landscape by creating and defining Threat Profiles and apply top-level filters for target Industries and target Regions. TTP Analysis feature helps users explore Threat Actors and Malware on the basis of the MITRE ATT&CK Framework.
Framework.
Prerequisites
Access requires users have access, and a valid authentication. Users must be provided access and authentication from the organization’s administrator(s).
Steps
- On the main page of Google Threat Intelligence Platform, go to the Left Navbar to select Threat Landscape.
- In the dropdown menu, select TTP Analysis to display the Explore MITRE ATT&CK page, explore threats in terms of adversary Tactics, Techniques, and Procedures (TTPs) based on real-world observations.
- At the top-left of the page, users can choose to explore:
- Actors

- Malware

- Actors
- To view Actors, users will select Actors in the Actor Selection page, which will display all Actors currently tracked by Google Threat Intelligence.
- Users will see three sections in the Explore MITRE ATT&CK page:
- Selected Actors
- Filters
- Threat Actor List
- In the Selected Actors section, users can select Add All to select all Actors. This displays all Actors currently tracked by Google Threat Intelligence.
- To remove all Actors from the Selected Actors section, users will select Remove All.
- In the Filters section, users can select the following Filters:
- Search Query
- Last Reference Date
- Source Region
- Target Industry
- Target Region
- Associated Malware
- Associated Tools
- The Threat Actor List is similar to the Threat Actors section of the Threat Landscape feature, but have different selection functionality.
- On a Threat Actor’s card there are two options to select:
- View Details
- Select
- Users select different Threat Actors from the Threat Actors List, by clicking the Select button on the Threat Actor Card.

- Once users select a card to be part of their TTP Analysis, they see it selected by observing the Selected button.

- All of the Selected Actors will appear in the Selected Actors section at the top of the page.

- Once all Threat Actors are selected for analysis, users will go to the Actor Selection and Analysis section at the top-right corner of the screen. In the Actor Selection page, users will see the Actor Selection button highlighted in blue.

- Users will select Analysis, when ready to observe the relevant TTPs, displayed in a MITRE ATT&CK framework.
- Users will see four sections in the Analysis page:
- Selected Actors
- TTP count by Actor
- Download TTPs
- MITRE ATT&CK Framework
- In the TTP count by Actor section, is a key that will show a color code representing the TTPs in the form of a Heatmap, where users can see shared TTPs used by the Selected Actors.
- As an example, users can see that there are shared Techniques between two Selected Actors.
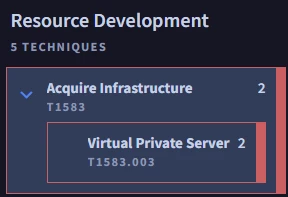
- This is done to show users the possible techniques to prioritize, or for Analysis of Competing Hypotheses.
- Users are able to download the Selected Actors TTPs, in the form of a .csv file, by selecting Download TTPs, in the top-right of the Analysis page.
Relevant Documentation Links
- All Steps: https://gtidocs.virustotal.com/docs/ttp-analysis
- Additional Documentation: https://gtidocs.virustotal.com/docs/ttp-analysis#to-filter-and-analyze-threat-actors
- Additional Documentation: https://gtidocs.virustotal.com/docs/ttp-analysis#analyze-malware-using-the-explore-mitre-attck-dashboard
Next Step: Google Threat Intelligence: Step 1.4 - Direction | Attack Surface Management
Previous Step: Google Threat Intelligence: Step 1.2 - Direction | Admin Setup
