Author: Jose Luis Sanchez Martine - Senior Security Engineer, Google Threat Intelligence
For intelligence analysts, tracking cybercrime actors on the dark web is an extremely labor-intensive and often frustrating process.
The complexity is constantly growing due to the proliferation of cybercrime forums dedicated to various activities, including carding, shops selling different types of data, leaks, and exfiltrations. This tracking challenge is further exacerbated when many forums are seized in joint law enforcement operations, only to have new forums quickly emerge, making continuous monitoring far more difficult.
In this blog post, we will share real use cases from our internal investigations demonstrating the power of GTI Agentic and the recently launched Dark Web (DDW) module. We have also enabled new modifiers to enhance search capabilities within the platform.
Agentic and the new DDW module allow us to perform hunting and pivoting much more easily, using either natural language or specific modifiers for complex scenarios that AI cannot currently address. It’s really straightforward and handy since we’re actively pulling in data from all sorts of forums and sources. Instead of having to bounce from one forum to another, you can just use these features to streamline your ongoing investigations.
Understanding Dark Web Forums
Tracing how underground cybercrime forums evolve shows that the real challenge isn't just shutting them down, it's the fact that they almost always come back. It's a constant game of whack-a-mole: a big forum gets taken down, the users scatter for a bit, and then, like clockwork, it pops up again under a new name with all the same illegal content.
The history of the dark web is littered with examples of "brand reincarnation," where a forum's reputation is so valuable that administrators or their successors prioritize rapid restoration over true anonymity.
The Successor Strategy: BreachForums
Perhaps the most modern example of this cycle is BreachForums. Following the seizure of RaidForums in April 2022, BreachForums emerged as its direct spiritual and technical successor. Even when the FBI arrested its founder in early 2023, the community did not dissolve. Instead, it migrated to new infrastructure under a rotating cast of administrators—including the "ShinyHunters" group. In May 2024, law enforcement again seized its domains, yet the forum reappeared on the clearnet within weeks, claiming to have regained control from the registrar.
The Migration and Rebrand: XSS.is (formerly DaMaGeLaB)
The longevity of XSS.is highlights how a forum can survive for decades by simply changing its name and domain. Originally established in 2013 as DaMaGeLaB, the forum faced a major crisis in 2017 when its administrator was arrested. Rather than disappearing, the platform was purchased, rebranded as XSS, and reactivated on a new domain in late 2018. Even after the recent July 2025 arrest of its latest administrator and the seizure of the xss[.]is domain, the forum persists through pre-established mirrors and onion addresses.
In fact, a very simple and clear example of understanding how some of these forums have been operated is through Agentic. We wanted to ask the question: 'How many breachforum sites existed until today?', and we obtained the following response.
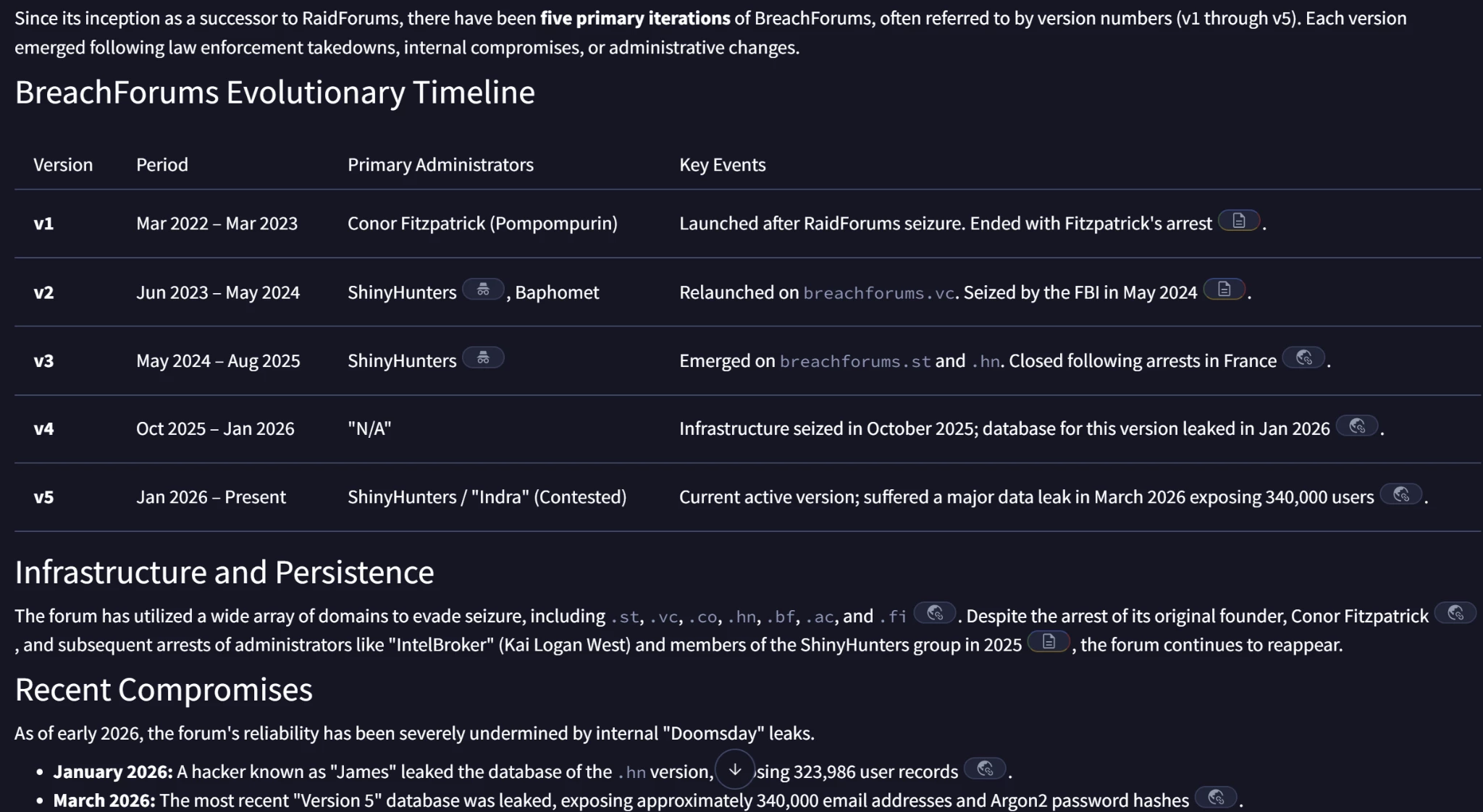
Figure 1: Automated timeline of BreachForums domain migrations and seizures generated by Agentic.
Case 1: From Infrastructure Buyer to Data Broker: A Multi-Alias Dark Web Investigation
In the complex ecosystem of the dark web, threat actors often maintain separate personas to segregate their "business" activities. Tracking these actors across disparate forums like Exploit, BreachForums, and Spear.cx usually requires weeks of manual cross-referencing. In this case study, we demonstrate how Google Threat Intelligence (GTI) Agentic can accelerate this process, moving from a single username to a comprehensive map of a global data exfiltration operation in minutes.
The Starting Point: Investigating "pepela"
The investigation began with a query about the user pepela, a handle active on the Exploit forum (exploit.in and exploit.biz). Initial findings characterized this user as a buyer of digital services, specifically involved in a $100 arbitration dispute regarding AWS accounts with another user named McCallister.
Pivoting on Cryptographic Metadata
The breakthrough occurred when Agentic identified a specific Tox ID shared by pepela while they were seeking high-volume SMTP services (capable of sending 500,000 to 1 million emails):
TOX ID
9073831FC539B084DA7DD270AC226EB7BF33F74AF517AA80BDFFD21105B6950AC811C66F4A8B
By pivoting on this unique identifier and a shared Session ID (05d847c329f5b6c8301bf358ba088dc30d5acd148ed77388350555fe754df95f59), Agentic definitively linked pepela to a much more dangerous alias: Spirigatito.
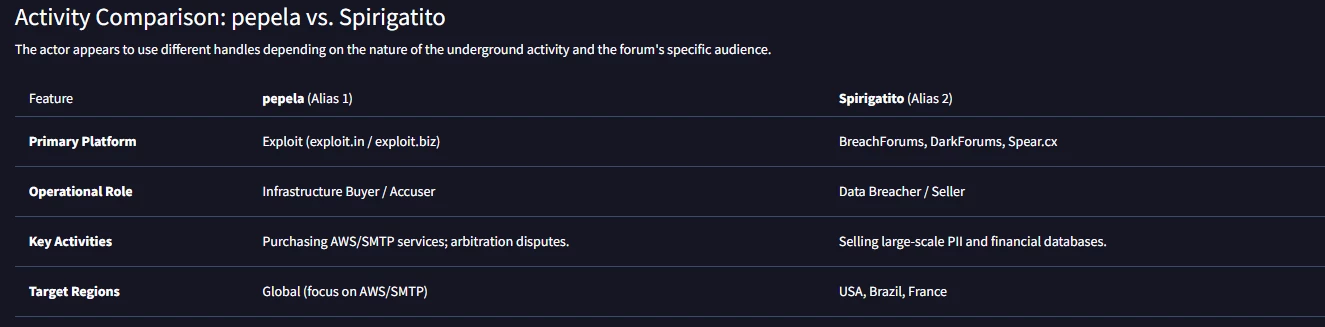
Figure 2: Table comparing activity related to pepela and spirigatito personas.
Mapping the Pipeline: Infrastructure vs. Monetization
The identification of the Spirigatito alias transformed the investigation. While pepela was the "buyer" persona used to acquire delivery infrastructure like Amazon SES, Spirigatito was the "seller" persona active on BreachForums and DarkForums, responsible for massive data leaks.
Notable exfiltrations attributed to this actor include:
- Infutor (USA): 676 million unique American records, including SSNs.
- Bebunk (France): A 200 GB breach of payment services involving 75 million rows of data.
- Tanzania BRELA: 10.2 million records exfiltrated in March 2026.
The Value of Agentic for Analysts
This investigation highlights the "Infrastructure-first" Modus Operandi of modern actors. Agentic allows analysts to:
- Bridge Identifies: Automatically link aliases across forums through shared contact details (Tox, Session, Telegram).
- Anticipate Campaigns: The shift to the pepela alias to buy massive SMTP infrastructure in early April 2026 suggested a new campaign was imminent.
- Visualize Relations: Generate immediate relationship graphs that map victims, modus operandi, and technical infrastructure back to the actor.
Automated Visualization: Mapping the Threat Landscape
One of the most powerful features of Agentic is its ability to generate instant visualizations of threat intelligence data. Instead of sifting through thousands of forum posts, analysts can request a relationship graph to see the "smoking gun" links at a glance.
For example, Agentic can output Graphviz or Mermaid code to map out the connections between aliases, shared identifiers, and victimized organizations. This allows for immediate identification of the actor's entire operational pipeline, from the infrastructure they buy to the datasets they sell.
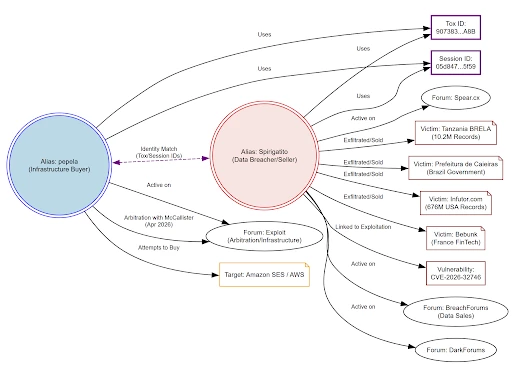
Figure 3: Relationship graph mapping the bridge between infrastructure acquisition (pepela) and data monetization (Spirigatito).
Link to Agentic conversation.
Case 2: Proactive Threat Hunting in the Financial Sector
In the world of corporate security, the "unknown unknowns" are the most dangerous. For a security analyst at a global institution like Banco Santander, the challenge isn't just finding if data has been leaked, but identifying exactly who is selling it, where, and whether the data is actually legitimate. In this case study, we walk through a real investigation where Agentic was used to map out the threat landscape targeting a major financial group.
The Analyst’s Query
The investigation began with a direct, high-level request to GTI Agentic: "I'm part of the Banco Santander Group and I would like to know if there are threat actors exfiltrating information from my company in the dark web". The system processed this high-level query rapidly, identifying several high-risk campaigns that would typically require hours of manual forum crawling.
Identifying the "Usual Suspects"
Agentic identified a diverse cast of threat actors operating across different niches of the underground economy:
-
Bancoscape (via DarkByte0x0): A specialized group on the Dread forum targeting High-Net-Worth Individuals (HNWIs) within the Spanish banking sector.
-
IntelBroker & Associates: Famous for the Cisco systems breach, which directly impacted Santander’s IT infrastructure arm, Produban.
-
SantaServices: A broker on the Russian-language XSS forum selling massive consumer databases that included thousands of Santander lines.
-
PoliceEspDoxedBF: An actor targeting Spanish government and law enforcement, whose leaks inadvertently exposed the personal banking details of officials holding Santander accounts.

Deep Dive: Verifying the "Smoking Gun"
One of the most critical steps for an analyst is verifying the "freshness" and legitimacy of leaked data. Often, actors "bluff" by recycling old leaks.
Agentic performed a deep-dive analysis into sample data provided by these actors, focusing on unique organizational identifiers and data structures that confirm the data's authenticity.
The investigation confirmed several high-fidelity matches:
-
A government-related leak included standardized financial account strings .
-
A leak by the actor Gumball contained valid financial identifiers, though Agentic noted some inconsistencies in categorization.
-
An Eni Plenitude breach included multiple confirmed accounts, including those of corporate entities.
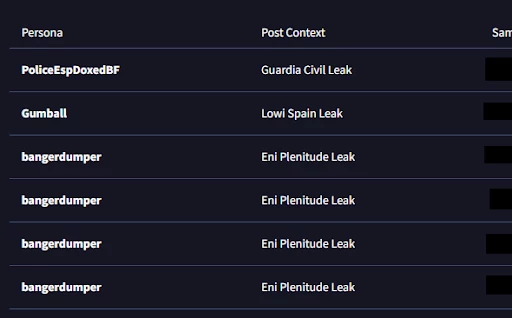
Figure 5: Automated analysis of dark web data samples verifying the legitimacy of Banco Santander standardized financial account strings.
The Analyst's Verification Workflow
For a financial analyst, the "pivoting" capability of Agentic allows for a two-tier verification process. First, the platform identifies the specific business units affected. In the Cisco breach, Agentic isolated data belonging to the specialized IT infrastructure arm of the group. This pivot allowed the security team to narrow their focus to internal infrastructure risks rather than just broad consumer data.
Second, Agentic automates the verification of assets. By automatically scanning sample dumps for specific organizational markers and technical metadata, the platform confirmed that the data from various leaks was high-fidelity and required immediate action.
Turning Data into Actions
By the end of the session, we moved the conversation with Agentic from a general concern to a structured list of Request For Information (RFI) items for a possible HUMINT team. These included identifying specific "internal banking system" vulnerabilities claimed by certain actors and investigating whether exposed source code contained hard-coded production credentials.
Case 3: How Agentic Exposed the Common Patterns of a Global Data Broker.
For threat intelligence analysts, the ability to connect seemingly disparate leaks to a single coordinated operation is the "Holy Grail" of attribution. In this case study, we demonstrate how GTI Agentic was used to unmask a prolific threat actor known as Grubder, revealing a sophisticated network of aliases targeting organizations globally with a highly standardized exfiltration pipeline.
The Starting Point: Grubder’s Prolific Activity
The investigation began by analyzing the dark web activity of Grubder, an actor focused on the sale of large-scale datasets from diverse international organizations. Grubder’s postings on platforms like darkforums.su covered sectors ranging from e-commerce and healthcare to education across Russia, Japan, South Korea, Spain, and the UK.
Figure 6: Original post identified in Google Threat Intelligence related to the user Grubder
Technical Fingerprinting: The CRM Connection
The investigation into Grubder revealed a highly professionalized methodology that differs from common "web scraping." Analysis of the exfiltrated headers showed the persistent use of the __c suffix. This is a technical artifact specific to Salesforce custom fields, proving that the actor possesses specialized tools to exploit cloud-based CRM connectors like Salesloft or Drift.
Furthermore, the connection between the various aliases was not based on "guesswork" but on a hard technical link: the reuse of a unique Session ID (0553ccc38730bd97ed3f05dddb34cc192b33a0392ad0c9cd319921351e6b9ebc10). This ID served as the "smoking gun" that tied the Russian-market leaks of Grubder to the Middle Eastern and European operations of batnetworkb_f.
Connecting the Dots: Linking Grubder to TelephoneHooliganism
While hunting for similar patterns, Agentic identified another persona, 'TelephoneHooliganism,' utilizing a nearly identical data structure for their sales.
By cross-referencing their marketing infrastructure, Agentic identified several "smoking gun" links:
-
Verbatim Marketing Templates: Both actors used identical phrasing in their posts, including a recurring claim that every dataset "Includes direct contact details, project descriptions, and funding amounts," even when irrelevant to the target sector.
-
Shared Session ID: The use of a specific Session ID (0553ccc38730bd97ed3f05dddb34cc192b33a0392ad0c9cd319921351e6b9ebc10) served as a definitive link between the personas.

Figure 7: Comparison made by Agentic regarding the two investigated personas.
The Broader Network
The investigation ultimately revealed a multi-persona infrastructure designed to scale data sales across different dark web forums after asking to discover more profiles. High-confidence aliases linked to this operation include:
-
gtaviispeak: Focused on Italy and SE Asia targets.
-
batnetworkb_f: Acting as a "regional manager" for European and Middle Eastern targets, sharing the same Session ID.
-
Badnigger_0004: Primarily targeting Chinese e-commerce entities.
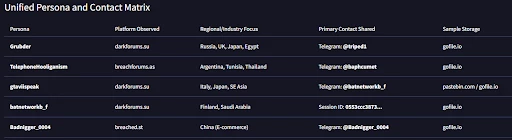
Figure 8: Comparison made by Agentic regarding the two investigated personas with their shared handles.
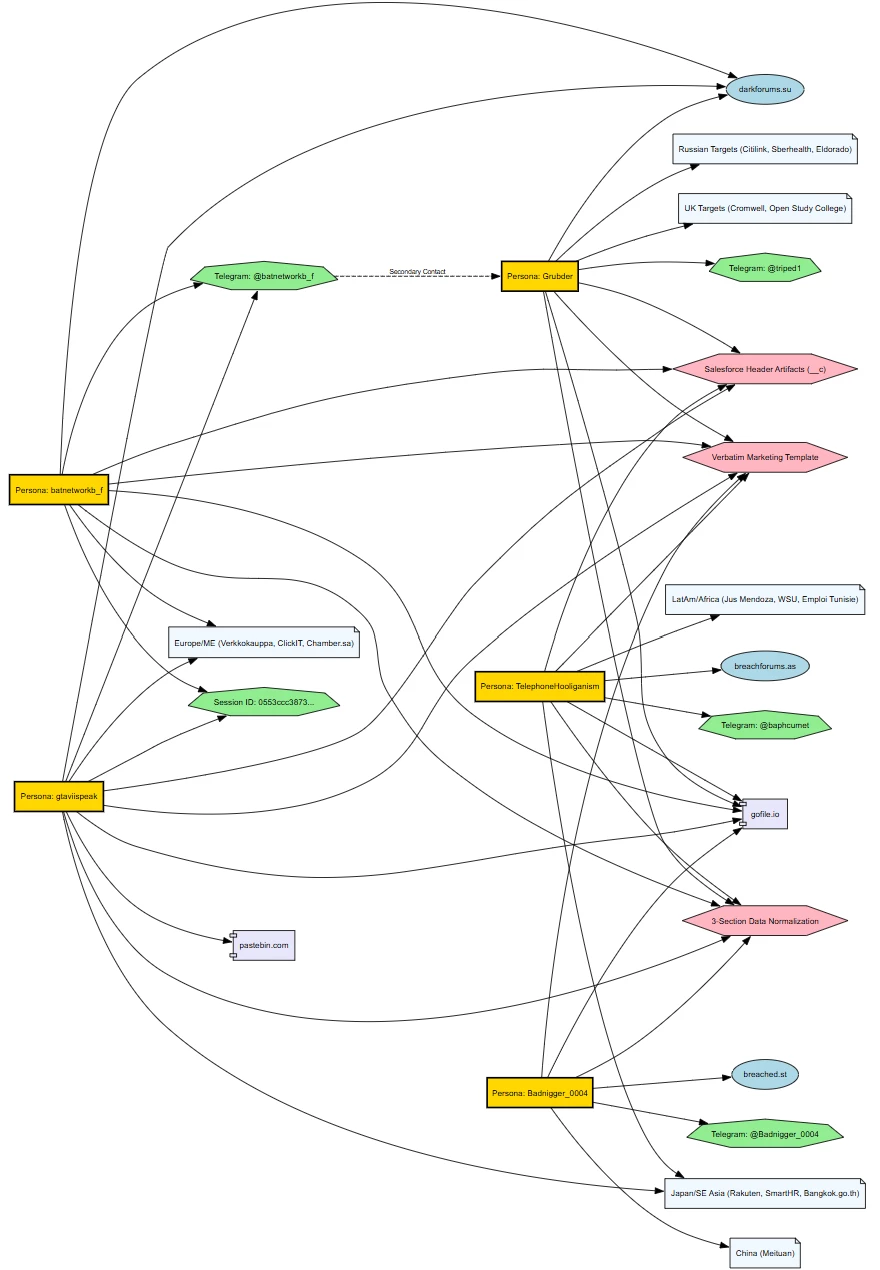
Figure 9: The automated "Hunt and Pivot" workflow demonstrating the transition from broad entity searches to attributed exfiltration posts.
Conclusions
The integration of GTI Agentic and the Dark Web (DDW) module transforms the often labor-intensive and frustrating process of underground monitoring into a streamlined, high-fidelity operation. By automating the correlation of disparate data points, analysts can move beyond manual forum crawling to a strategic understanding of threat actor lifecycles.
As demonstrated through the cases of pepela, Banco Santander, and Grubder, these tools provide critical advantages for modern defense:
-
Automated Attribution: By identifying persistent technical fingerprints—such as Tox IDs, Session IDs, and CRM-specific artifacts like the __c suffix—Agentic bridges the gap between seemingly unrelated personas and global exfiltration pipelines.
-
Surgical Precision: The DDW module's granular modifiers allow analysts to perform targeted "hunting" for specific leaks (e.g., LOWI Spain or CTT Express) and exfiltrated schemas, ensuring that the most critical risks are identified with surgical accuracy.
-
Actionable Verification: The ability to automatically verify the legitimacy of leaked data—such as bank-specific IBAN codes—empowers security teams to move immediately from investigation to targeted mitigation. Even if you are not familiar with that.
-
Visualizing the Network: Analysts can instantly generate relationship graphs that map the connections between infrastructure, victims, and threat actors, turning raw data into an immediate "smoking gun" visual.
It is important to note that these capabilities are currently in BETA, and we are continuously working on further improvements and feature expansions to stay ahead of the evolving underground landscape. If you have any suggestions or comments regarding the platform or these investigative workflows, we are open to receiving them.