Blog Authors:
Christiane Peters, Security Architect, Office of the CISO, Google Cloud
Stefan Kölbl, Information Security Engineer
The impending transition to post-quantum cryptography (PQC) is prompting organizations to understand where their current cryptography resides. While the immediate concern is PQC readiness, the lessons learned from past crypto migrations like Heartbleed and SHA-1 underscore a fundamental truth: knowing your cryptographic footprint is vital for agility and resilience. Instead of treating the creation of a crypto inventory as a one-off PQC project, Google advocates for embedding it within a broader strategy centered on robust key management and, ultimately, business continuity. By prioritizing the security and lifecycle management of cryptographic assets, organizations can not only navigate the PQC transition but also strengthen their overall security posture and ensure operational continuity in the face of future technological shifts.
The drumbeat for understanding your cryptographic landscape is growing louder. Regulatory bodies and industry experts worldwide are urging organizations to identify where their “cryptography” – specifically public-key cryptography for asymmetric key exchange and encryption – is being used. This call to action stems from the practical challenges encountered during previous cryptographic migrations. The painful lessons of identifying vulnerable OpenSSL libraries during Heartbleed or tracking down SHA-1 certificates highlighted a critical dependency: you can't migrate what you don't know.
Recognizing the complexity of modern IT environments, a market for "crypto scanners" and consultants has emerged to help organizations map their cryptographic assets. These solutions often provide valuable dashboards detailing keys, certificates, libraries, and algorithms. However, the critical question that follows such an inventory is: Then what?
At Google, we approached this challenge by focusing on the "then what" from the outset. Instead of solely concentrating on the quantum threat or a one-off PQC rollout, we integrated the need for migrating cryptography into a larger framework centered on business continuity and a well-defined cryptographic architecture. We recognize that the core of data protection lies in keeping cryptographic keys secure and effectively managed on the long run. We have linked the ability to seamlessly transition to new cryptographic algorithms – keyword “cryptographic agility” – tightly to robust key management practices, particularly key rotation as described in this Google blog post.
We don't just aim for a list of cryptographic elements; we strive for a comprehensive understanding of the entire key lifecycle and its context within the organization. Our methodology encompasses the following principles:
1. Robust Cryptographic Key Inventory
Following key management best practices, including those detailed in NIST SP 800-57, we begin with what we define as a robust inventory of all cryptographic keys and their management systems within Google. Our approach to building this inventory involves several key steps:
- Automated Classification of any New Keys: Newly generated keys are automatically captured, classified and their relevant metadata is stored within our systems in a unified structured form to be easily queried.
- Discovery and Classification of Existing Keys: For our existing key landscape across various keystores and even within codebases across Alphabet, we undertook an initial effort to gain broad visibility. This involved scanning and classifying keys, a process that presented challenges with some raw key material of undocumented formats. To address this, we developed common pattern recognition for our most frequently used key types. Our internal search tools have proven effective for a significant portion of these keys.
- Continuous Refinement through Metrics and Metadata: We continuously adapt our metrics and the metadata we collect to progressively improve the coverage and accuracy of our key inventory over time.
This multi-faceted approach allows us to build and maintain a strong understanding of our cryptographic landscape.
Beyond basic identification, a key inventory's true value lies in the contextual information – the metadata – associated with each key. To effectively identify dependencies and potential vulnerabilities, we meticulously extract and categorize critical key properties. This detailed metadata enables comprehensive analysis and includes:
- Key Identification, Ownership, Protection and Criticality: Unique ID, who is responsible for this key, where it is stored with which protection level, and an assessment of the key's overall importance to our operations.
- Key Access, Usage, and Life cycle: Authorized users, the applications and systems utilizing the key, when and where the key is used in deployed systems, and the full lifecycle of the key from creation, activation to deletion.
- Cryptographic Algorithms, Key Length, and Parameters: The actual cryptographic algorithm used, including parameters like key lengths and configured options.
To ensure the security and resilience of our cryptographic posture, our inventory also informs our processes for:
- Key Recovery and Compromise: Procedures for detecting potential key compromise and the established processes for key recovery or replacement.
Our inventory metadata strategy prioritizes this rich contextual information. For example, Google Cloud KMS provides detailed key attribute and usage information, illustrating the principle of documenting key purpose and application. While this example is specific to our cloud environment, the underlying principle of documenting key usage is universally applicable across any infrastructure. This comprehensive metadata, going beyond just a list of cryptographic assets and algorithms, allows for in-depth analysis and informed decision-making regarding our cryptographic posture.
2. Streamlined Algorithm Transition via Integrated Libraries
Our development practices mandate the use of Google’s cryptographic libraries, with the Tink crypto library as our primary choice for its developer-friendly nature and tight integration with our key management systems and monitoring solutions. The combination of these tools and systems enables reliable management of a cryptographic key’s lifecycle.
Tink simplifies algorithm transitions to a mere key switch, significantly minimizing the need for extensive application code modifications. For example, migrating digital signatures from ECDSA to ML-DSA becomes primarily a key rotation. This allows developers to concentrate on the effects of the new algorithm, like performance and latency, instead of the intricacies of the cryptographic change. This ease of use, while enforcing secure practices, allows developers to concentrate on ensuring their application functions optimally with the new performance profile and not worry about the underlying cryptographic properties. To learn more about our approach to cryptographic agility, read our blog post on Cryptographic Agility and Key Rotation.
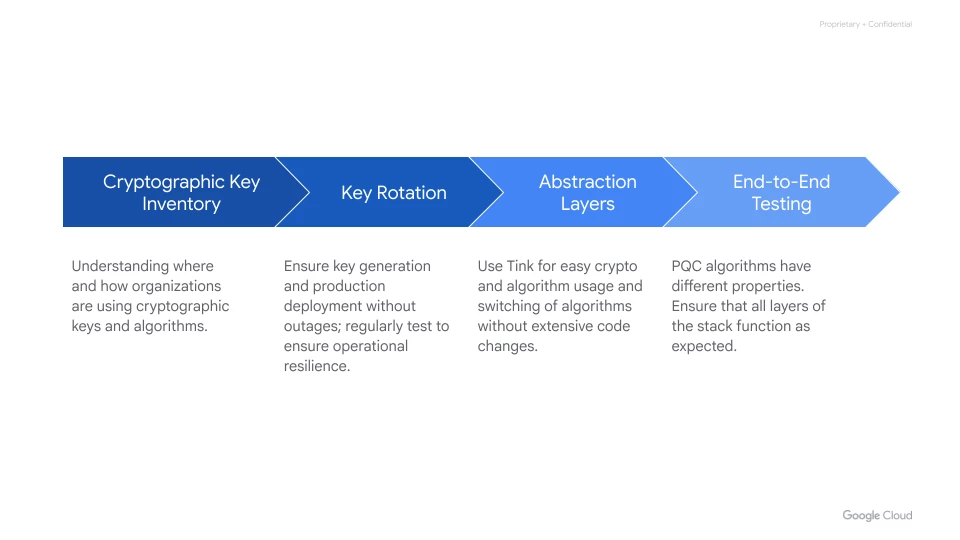 Image: How Key inventory fits into Crypto Agility Strategy
Image: How Key inventory fits into Crypto Agility Strategy
Beyond a Project: Robust Key Management for Business Continuity
The message for CISOs and teams is clear: a comprehensive cryptographic key inventory isn't merely a compliance exercise or a one-time project to prepare for quantum threats. Instead, it's an integral component of a robust automated key management framework, which is fundamental to business continuity and data security. While the Google Cloud stack offers inherent advantages, our core principles for establishing a robust key inventory and management strategy are applicable to organizations of all sizes and complexities.
By adopting the principles above, organizations can move beyond a reactive "crypto inventory project" towards a resilient and fully automated key management practice. This not only addresses the immediate need for PQC readiness and regulatory compliance but also solves the enduring "today problem" of ensuring the continuity and robustness of your data security posture. Thinking of the move to quantum-safe cryptography as an enterprise-wide initiative, deeply integrated with your key management strategy, is the most effective path to long-term security and agility.
Resources: