Blog Authors:
Ofir Rozmann, Principal Researcher, Google Threat Intelligence Group
Daniel Kapellmann Zafra, Intel Strategy Lead, Google Threat Intelligence Group
The complexity of modern malware has created a persistent gap between the volume of incoming threats and the time required for expert analysis. Traditional automation captures granular behaviors, but often lacks the context required to synthesize them into a cohesive attack narrative or durable detection logic.
By integrating agentic AI into the workflow, investigators can move away from tedious manual analysis and focus on decision-making. Agentic threat intelligence (TI) in Google Threat Intelligence reasons through code logic, complex file structures, and global intelligence repositories to present a clear, technical narrative in seconds, rather than hours. The acceleration of analyst workflows is a trend we have previously observed and described in our research on Gemini’s capabilities for malware analysis.
This blog provides a deeper dive into using agentic TI capabilities to conduct malware triage and analysis. It builds off our recent blogs on Operationalizing Agentic Threat Intelligence and Redefining Threat Intelligence with Agentic.
Submitting Files and Secure Execution
To begin analyzing a threat, analysts can provide a sample to agentic TI in two primary ways:
-
By Hash: This is the most efficient method for triaging samples already indexed in the global database and enables the user to obtain further insights into knowledge compiled from prior Google Threat Intelligence analysis. Agentic TI accepts MD5, SHA1, or SHA256 hashes without consuming Private Scanning quota.
-
By Upload: For novel or sensitive samples with intelligence gaps, you can upload files through the agentic TI UI or pivot from a Google Threat Intelligence Private Scan. This allows for a deeper level of inspection within seconds. This functionality supports compressed archives (ZIP, 7z, RAR) and will automatically prompt for a password if protected or attempt to unbundle the files using common passwords like 'infected' to reach the underlying payload.
Privacy and Secure Execution
- Confidentiality: Using Google Threat Intelligence, Private Scanning ensures the sample remains confidential and is not shared with the public community or used to train external AI models. See more information about our privacy settings in our Platform documentation.
- Context vs. Analysis: When you “upload a file as context,” the LLM parses the file's text (such as code snippets, logs, or an email body) to use as background for your prompt. Choosing the "analyze a file" option instead triggers a full dynamic execution in the secure sandbox to observe its behavior.
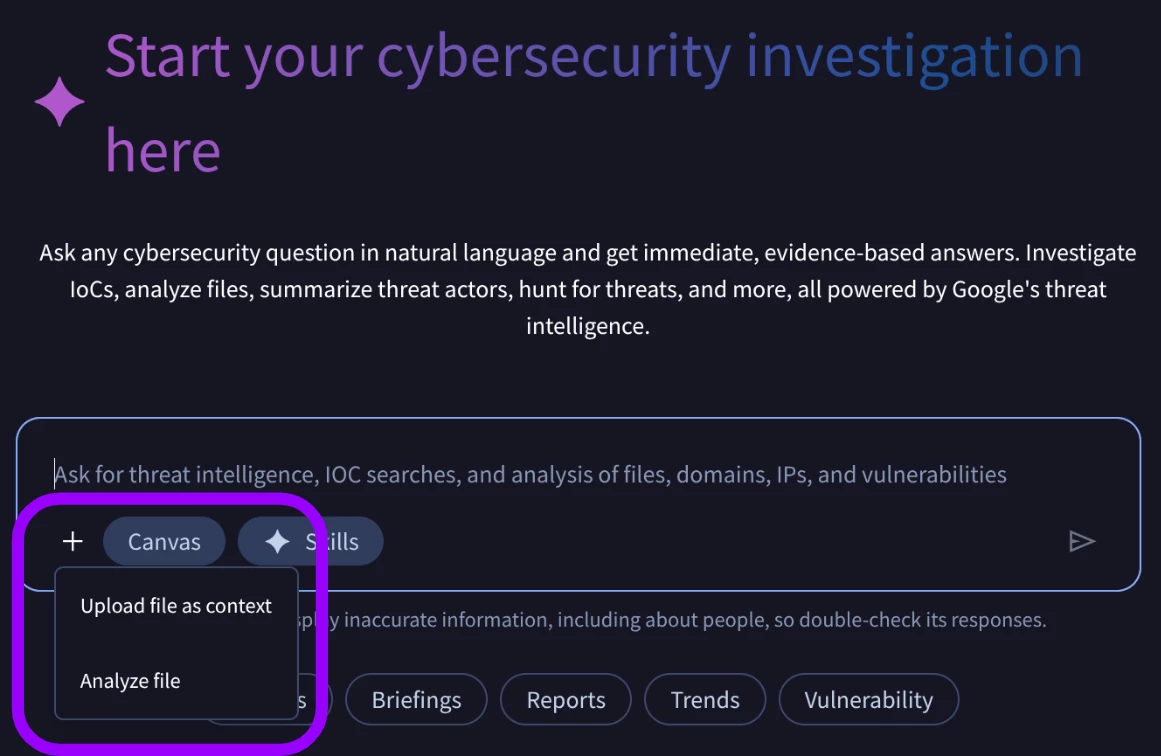
Figure 1: File upload options
(Note: Every file upload for dynamic analysis consumes a portion of your group's Private Scanning quota.)
Agentic Threat Intelligence: Core Capabilities and Deep Inspection
To trigger agentic TI malware triage and analysis capabilities, a user can directly input a prompt in the UI to request the analysis of a sample, or generate a triage report via the Brief button found in the Public and Private Scanning upload pages.
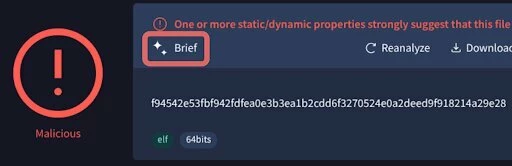
Figure 2: Screenshot of the Brief button available in Public and Private upload page
Comprehensive Binary Analysis
By requesting a “deep-dive analysis,” analysts can initiate investigations into logic flows and code citations across an extensive range of compiled formats. The malware analysis agent supports a comprehensive list of executables, including PE binaries (such as those compiled with Go and .NET), ELF binaries, as well as Java archives (JARs) and Android executables (DEX). Furthermore, the agent identifies the underlying file structure and packaging of an executable to optimize analysis. For example, when analyzing an AutoIt3 compiled binary, it will intelligently extract and decompile the underlying script instead of focusing on just standard PE disassembly.
Figure 3: Screenshot of the Reverse Engineering Analysis
Format Support & Behavioral Triage
Agentic TI provides deep visibility across an extensive range of modern delivery vectors. Some examples of supported categories include:
- Scripts & Interpreted Languages: Immediate insights into the intent of PowerShell, VBScript, Python, etc.
- Documents & Productivity Tools: PDFs, RTFs, and Microsoft Office formats.
- Archives & Disk Images: The ability to unpack standard archives and disc images like .zip, .rar, .iso, and .vhd files.
- Mobile & Email: Android (APK, DEX) and email objects (.eml, .msg).
Malware Triage & Analysis In Action
These sample case studies show how the agentic capabilities accelerate investigations by correlating code analysis with sandbox results and threat intelligence. We are continuously refining these capabilities.
Case Study 1: Unknown ELF File
As part of threat hunting, an analyst encountered an unknown ELF file, with no available data in Google Threat Intelligence.
-
Sha256: f94542e53fbf942fdfea0e3b3ea1b2cdd6f3270524e0a2deed9f918214a29e28
-
MD5: d02421aa7b21a170bb8f92d9326e5745
The analyst submits the file to Google Threat Intelligence Private Scan, which provides a verdict of the file being malicious. Subsequently, the analyst requests a Brief, which triggers agentic TI to analyze the file and return Google Threat Intelligence private sandbox results, providing details and preliminary analysis.
-
Near-instant verdict: The malware analysis agent identifies the file as a 64-bit ELF binary and confirms its malicious intent through detections and behavioral analysis, noting that it executes unauthorized commands and interacts with system logging utilities and sensitive files.
-
From Triage To Mitigation: The analyst then submits a prompt to agentic TI requesting an executive brief. The output provides recommendations to mitigate the threat based on the file behavior, ranging from hunting for the activity in logs to hardening the environment and host configurations.
Operational Outcome
The agentic capabilities allow the analyst to provide a near-instant malicious verdict on a previously unknown file not indexed in Google Threat Intelligence, with no available open source intelligence. The agent’s analysis and recommendations are subsequently leveraged to implement a plan of action to further hunt and mitigate the threat - from a local, immediate response, to a full escalation if needed. Although in-depth manual reverse engineering may be necessary in some cases, this initial triage enables defenders to significantly shorten the time-to-action in the face of malicious, unknown behavior.
Case Study 2: SELFDRIVE – Synthesizing Existing Intelligence
During routine endpoint monitoring, an analyst identifies a heavily obfuscated Node.js script.
- SHA-256: dd8502622eaa4e3798f4848cfe81c06ed0dffd7cb0a62c7ab6c7124d5b07bb04
- MD5: 61a47f0fde90832c14c148ab54829ac7
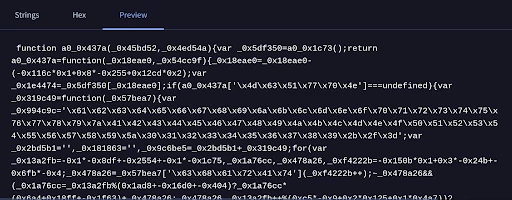
Figure 4: Screenshot of the obfuscated Node.js script
The analyst queries the hash in agentic TI and requests a Brief. Since the file is already indexed in Google Threat Intelligence, the triage agent rapidly synthesizes existing global intelligence to perform behavioral triage. It identifies the script as the SELFDRIVE backdoor, attributed to the threat actor UNC6448. The analysis agent recognizes that this malware is frequently bundled within trojanized installers for legitimate software and proceeds to map out its logic.
-
From Code to Intent: The analysis agent decodes the obfuscation layers to reveal a sophisticated profiling routine, identifying that the script profiles the host system by querying MachineGuid from the Windows Registry. It extracts a hardcoded HTTPS C2 endpoint (api[.]vtqgo0729ilnmyxs9q[.]com) used for beaconing. The agent then enriched and corroborated the results of its analysis with pre-existing sandbox results.
-
Contextual Logic Extraction: The analysis agent identifies the script's capability to download and execute XOR-encrypted, Base64-encoded payloads. By identifying the use of the eval() function, the agent confirms the malware's ability to execute arbitrary code directly in-memory, bypassing traditional disk-based detection.
Operational Outcome
Armed with the deobfuscated C2 domain, the execution behaviors, and the root-cause delivery URL, the analyst executes a rapid, multi-tiered response. After querying the SIEM to confirm no successful beaconing occurred to api[.]vtqgo0729ilnmyxs9q[.]com, the analyst isolates the affected endpoint to preempt any stage-two payload deployment. Concurrently, they block both the C2 domain and the spoofed download site at the network perimeter, effectively neutralizing the campaign across the enterprise. Finally, to address the root cause, the IR team leverages the incident to issue a targeted advisory, enforcing the internal policy that all corporate utilities must be provisioned exclusively through the company's vetted self-service software center.
Case Study 3: POISONPLUG – From Analysis To Detection
A researcher encounters a suspicious SFX archive, which extracts a legitimate Windows binary alongside unknown files.
-
SHA256: 4d7da83ed24320959b067e0ac9682fadc3536e48a4d1290987b4e2991be9c0a3
-
MD5: 855b67dcf9be43f6e92e41e18c1ae64d
The researcher provides the MD5 in agentic TI to analyze the sample, attribute it to a specific malware family, and assist in follow-up remediation and detection.
Drawing on existing Google Threat Intel corpus data, the analysis agent identifies the sample as a POISONPLUG loader, analyzes its installation process and identifies IOCs. POISONPLUG is a sophisticated, modular remote access trojan (RAT) commonly used by China-nexus threat actors, known for its use of DLL sideloading to bypass security software and maintain long-term persistence.
-
Infection Chain: Analyzing the SFX file contents and host-based artifacts obtained by the sandbox results, the agent recognizes a three-file DLL sideloading pattern. It identifies that the launcher (a renamed legitimate executable) is being abused to load a malicious DLL (imjp14k.dll), which then decrypts a hidden payload. By connecting these disparate events: file drops, service creation (NetworkSrv), and registry modifications, the agent reconstructs the full life cycle of a POISONPLUG infection.
-
Artifact Extraction: Moving beyond the initial analysis, the agent extracts host and network based IOCs, which could then be leveraged to detect the activity, or curate host or network based detection rules.
Operational Outcome
Following the discovery of a new POISONPLUG infection, the organization initiates a containment and eradication protocol. After cross-referencing the MD5 hash and the malicious imjp14k.dll against EDR telemetry to identify any potential infections, the analyst triggers an automated isolation of all hosts exhibiting the unauthorized service creation. To mitigate the risk of future sideloading exploits, the IR team updates the enterprise application control policy to enforce strict DLL signature validation and implements a proactive hunt for non-standard binaries residing in sensitive system directories.
Case Study 4: APT29 – Malicious Email Triage & Mitigation
During a compromise assessment, a CTI analyst identified a spear-phishing attempt utilizing a social engineering lure:
- SHA-256: 6b0bd7937e6da617eefc4d8e237b34695419d1abff7da2971b8c4e0249f5c9b4
- MD5: 6ed7079ffa933174ebed856154b1c44b
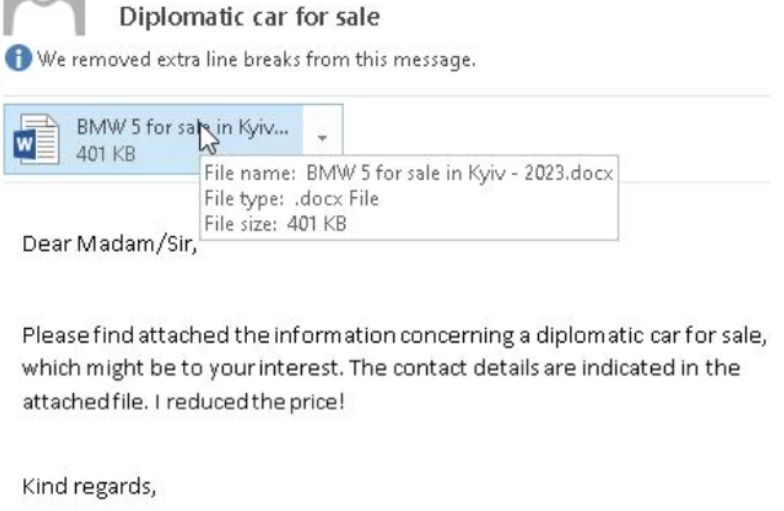

Figure 5: Screenshot of the phishing email and decoy document
The analyst asks the analysis agent to investigate the suspicious email hash. By parsing available public reporting and existing global telemetry, the agent identifies the email as a delivery vehicle for Russia-nexus malware attributed to APT29. The agent identifies the campaign's focus on European diplomatic missions and proceeds to deconstruct the multi-stage infection vector.
-
Decoy Analysis: By analyzing the document's external relationships, the agent identifies template injection using a URL shortener (t.ly) designed to fetch a secondary payload, bypassing static attachment scanning.
-
Contextual Logic Extraction: The agent identifies the use of DLL Side-Loading, where a renamed legitimate executable (windoc.exe) is used to side-load a malicious DLL (AppvIsvSubsystems64.dll). It links the attack to Google Threat Intelligence and public reporting, and is able to identify the final backdoor that uses trusted services for C2 communications.
The preliminary analysis can be further enriched through targeted prompts that extract granular intelligence on the campaign, threat actor profile, and historic activities sourced from Google Threat Intelligence and open-source intelligence (OSINT). In this case, following this initial assessment the user leverages agentic TI to formulate a comprehensive response plan.
Operational Outcome
Following the identification of host-based artifacts and the resetlocations[.]com C2 domain, the analyst initiates a comprehensive containment strategy. Beyond blocking the identified IOCs, the security team implements behavioral monitoring for any legitimate binaries executing from the $Recycle.Bin directory.
To mitigate future risks, the organization launches a targeted awareness initiative specifically for high-value diplomatic targets, focusing on the danger of "Special Interest" social engineering and the risks of LNK file execution.
Management is briefed on the risk of the potential attack, which uses trusted services for C2 and was identified only retroactively, leading to an audit of cloud-tenant permissions and the enforcement of stricter Office template policies to neutralize the threat's primary delivery mechanism.
Expanding the Agentic Approach for Malware Analysis
The transition from manual binary triage to automated, agent-led intelligence represents a fundamental shift in how we close the gap between threat volume and analyst capacity. Agentic TI does more than just supply data. It acts as a digital assistant that reveals the hidden logic of a binary, allowing investigators to move from "what is this file?" to "what is this code trying to achieve?" in a matter of minutes.
Acknowledging that sophisticated actors will inevitably develop techniques to subvert automated reasoning, we will proactively enhance agentic TI to adapt to upcoming threats. As we expand these capabilities and refine the analysis agent’s logic, we are moving toward a future where we empower analysts to perform deep, expert-level analysis at the speed and scale of the modern threat landscape.