Hi Community,
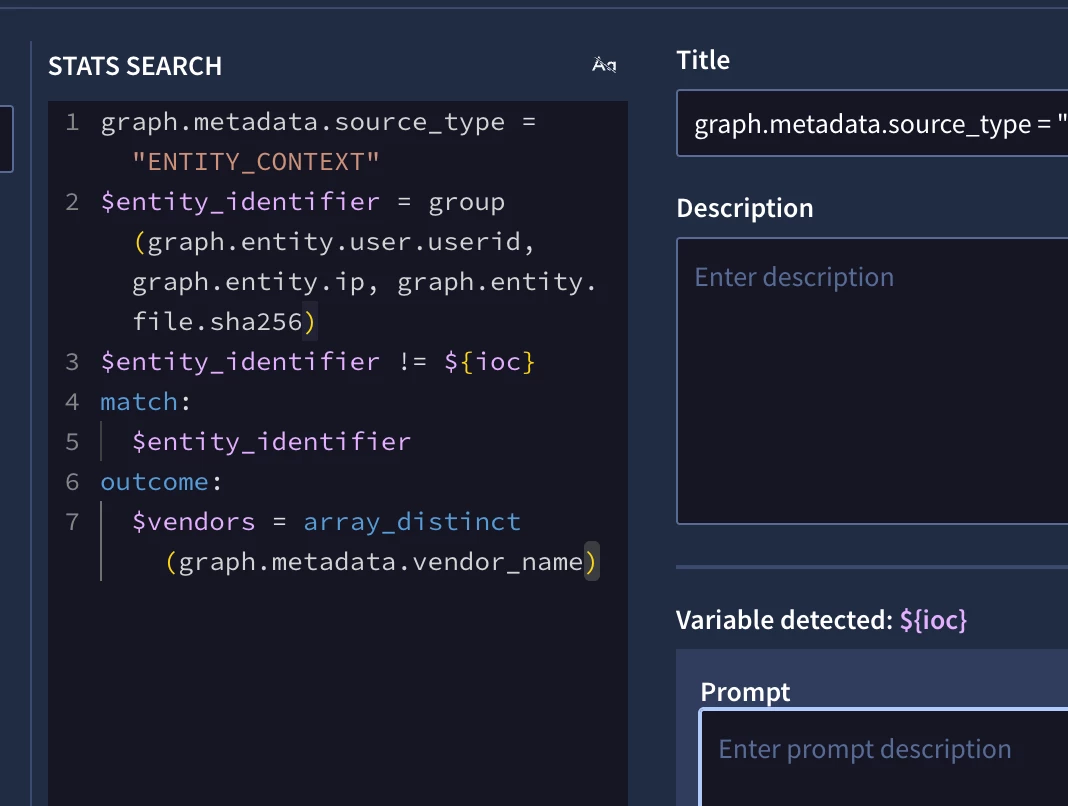
Our team is looking to build a unified dashboard in Google SecOps (Chronicle) that enables analysts to search for Indicators of Compromise (IOCs) across all available data sources from a single interface.
Use Cases:
- Username search: Enter a username and retrieve all events associated with that user across all ingested data sources within a configurable time range (e.g., last X days).
- IP address search: Query an IP address and see all related network activity, authentication events, alerts, etc.
- Hash value search: Look up a file hash and identify all occurrences across endpoint, proxy, and other relevant log sources.
Essentially, we're looking for a centralized IOC pivot dashboard that aggregates results from multiple log types and presents a consolidated view for faster investigation and threat hunting.