Hi everyone,
We are working on integrating Google SecOps SOAR with an external application security platform, and wanted to validate our approach as well as explore better alternatives.
Use Case
1. Incident Sync (Bi-directional)
- Sync status and comments:
- From SecOps SOAR → external platform
- From external platform → SecOps SOAR
Current Approach
- Using a scheduled job (polling) to:
- Fetch updates from both systems
- Compare changes
- Push updates accordingly
Questions
- Architecture Validation
- Is a polling-based approach considered acceptable for this use case?
- Or is any other approach recommended?
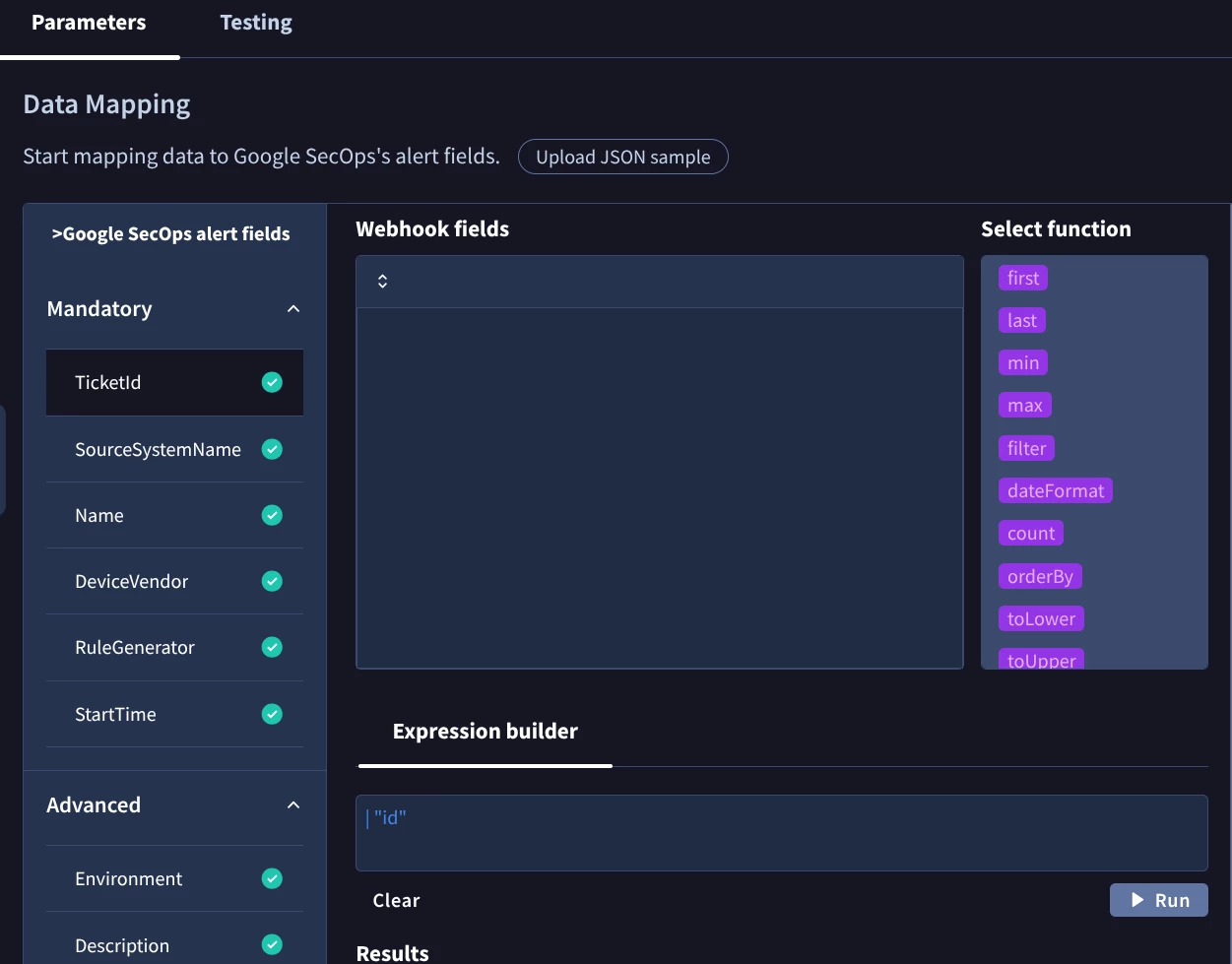
- Webhook Capabilities in SecOps SOAR
- Are there limitations on which fields can be mapped via webhook?
- Is it possible to map custom fields (status, comments, metadata)?
- Is there any reference for the list of fields.
- Comments / Notes Mapping
- In SecOps SOAR alerts, which field is best suited to store external comments/notes?
- Is there a recommended standard field (e.g., notes, activity log)?