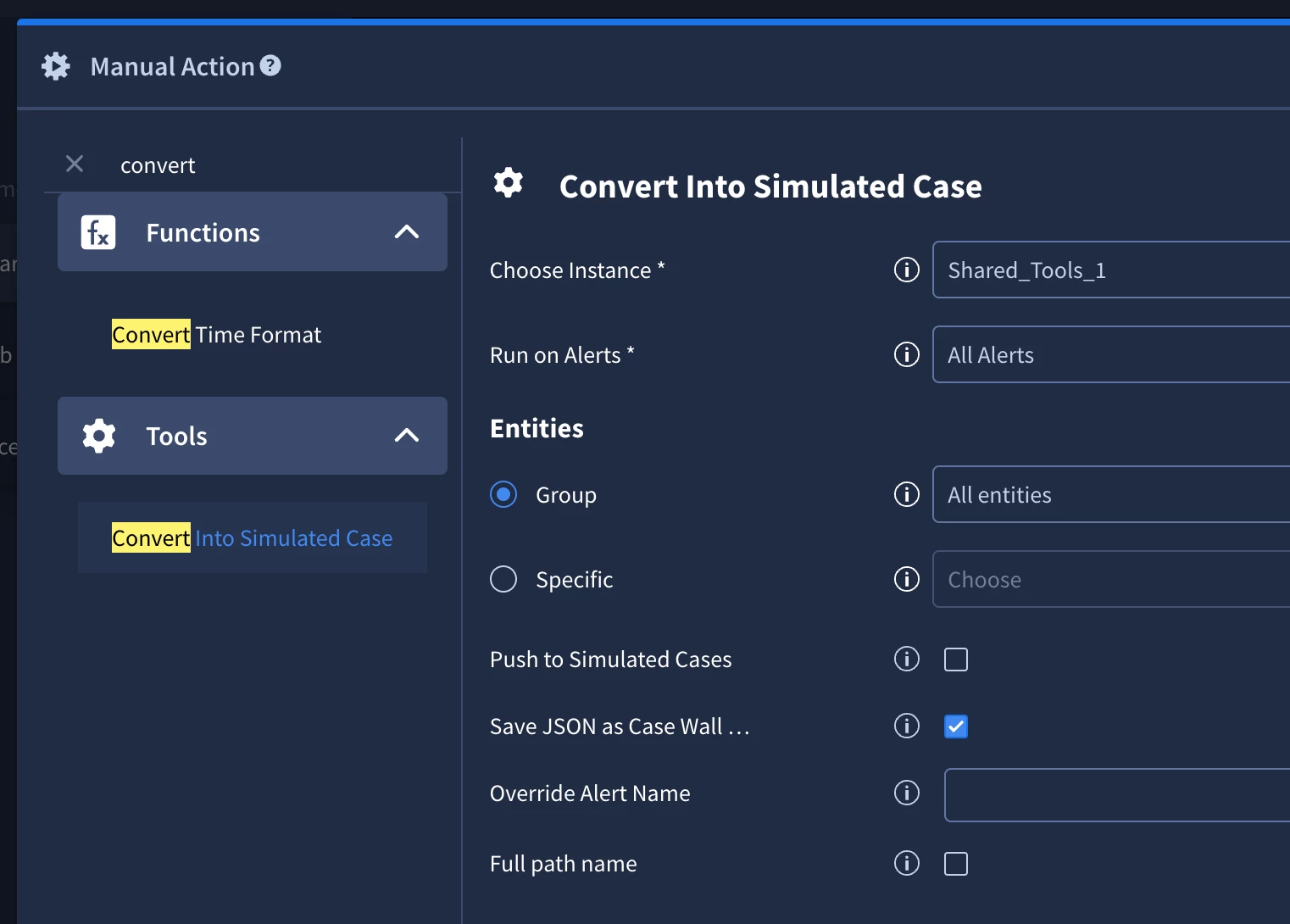
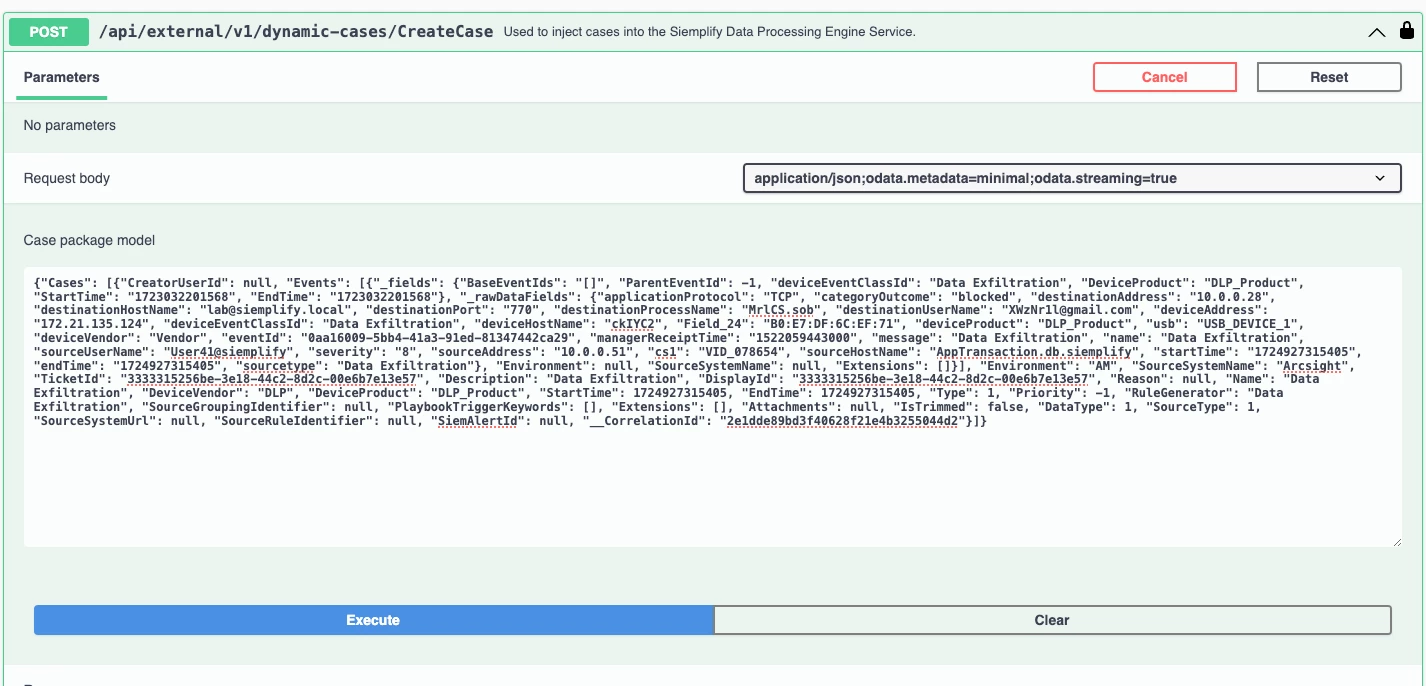
Is there any UI option available to achieve this task? if yes, please do let me know.
Solved
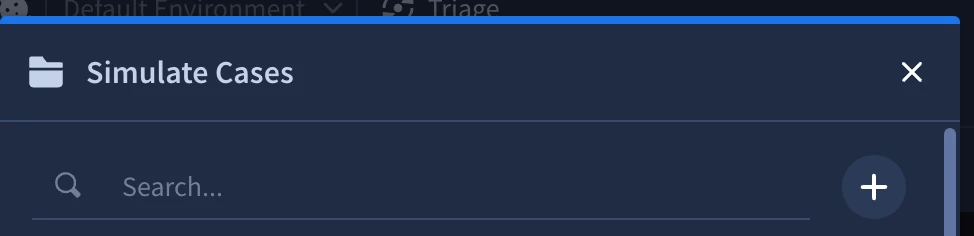
How to export Alerts and Cases from SecOps prod tenant and re-import it into Dev-tenant
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.