New to Google SecOps, so I might not be looking in the right place, hoping to get some help.
I setup 2 Feeds to pull from the Rapid7 Insight Cloud console one for assets and one for vulnerabilities.
https://docs.cloud.google.com/chronicle/docs/reference/feed-management-api#rapid7-insight
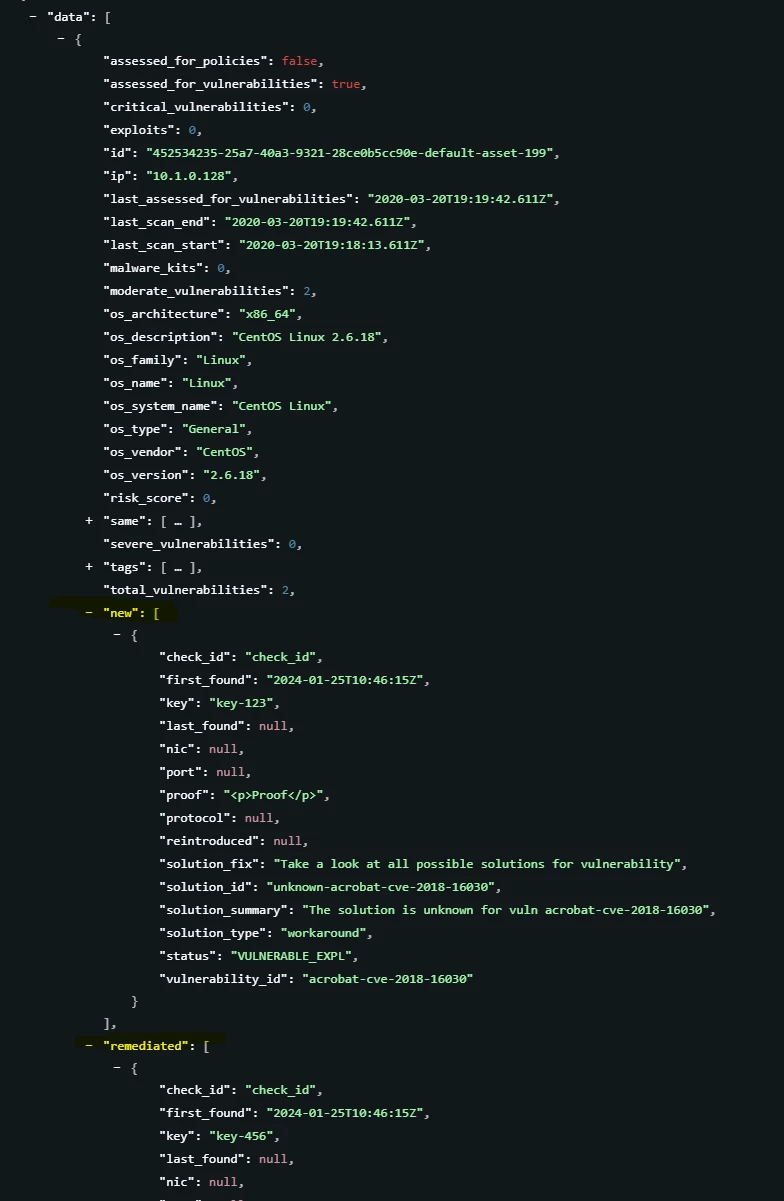
Data started to be ingested but there does not appear to be individual vulnerability findings per system.
There’s vulnerability definitions which just give you information on a vulnerability and then there is the asset information along with vulnerability information such as it has 10 critical but no information on what they are. There does seem to be a new[] and remediated[] field which is always empty even in the raw event.
Am I missing something to be able to get the actual vulnerability finding information? How have you configured your console to ingest this data?