Thanks, @f3rz , for the quick reply.
Yes, creating a new action is possible. However, after creating the integration, I will hand it over to the SOC analysts, who will create playbooks based on their use cases. They won’t have knowledge of how to create new integrations.
For the second question: from the documentation you shared, it states that you can select the required parameter. However, note that the drop-down will only show the script results from actions that are part of this playbook.
Previously, I created an playbook with Splunk SOAR, which provides the functionality mentioned above, independent of the integration. I wanted to check if Google SecOps SOAR has any native support for similar features.
Reference:
1. Custom Code Execution:https://docs.splunk.com/Documentation/SOAR/current/Playbook/CodeBlock
2. Capture Inputs:https://docs.splunk.com/Documentation/SOAR/current/Playbook/PromptBlock
1. You may explore the PowerUps we have. Some of them may transfer results from X to Y without requiring custom development. But if there's nothing for your usecase, there's no other choice rather than either request it as a Feature Request or make a custom action.
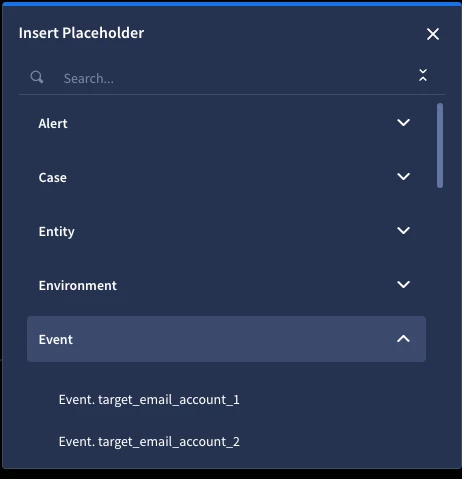
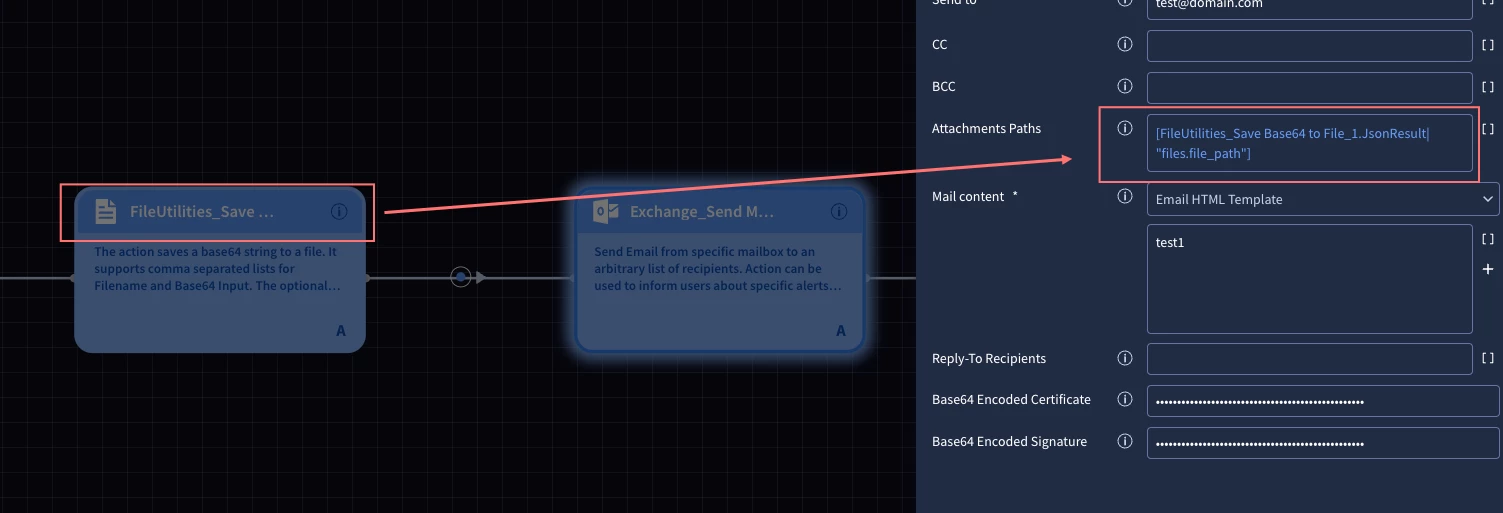
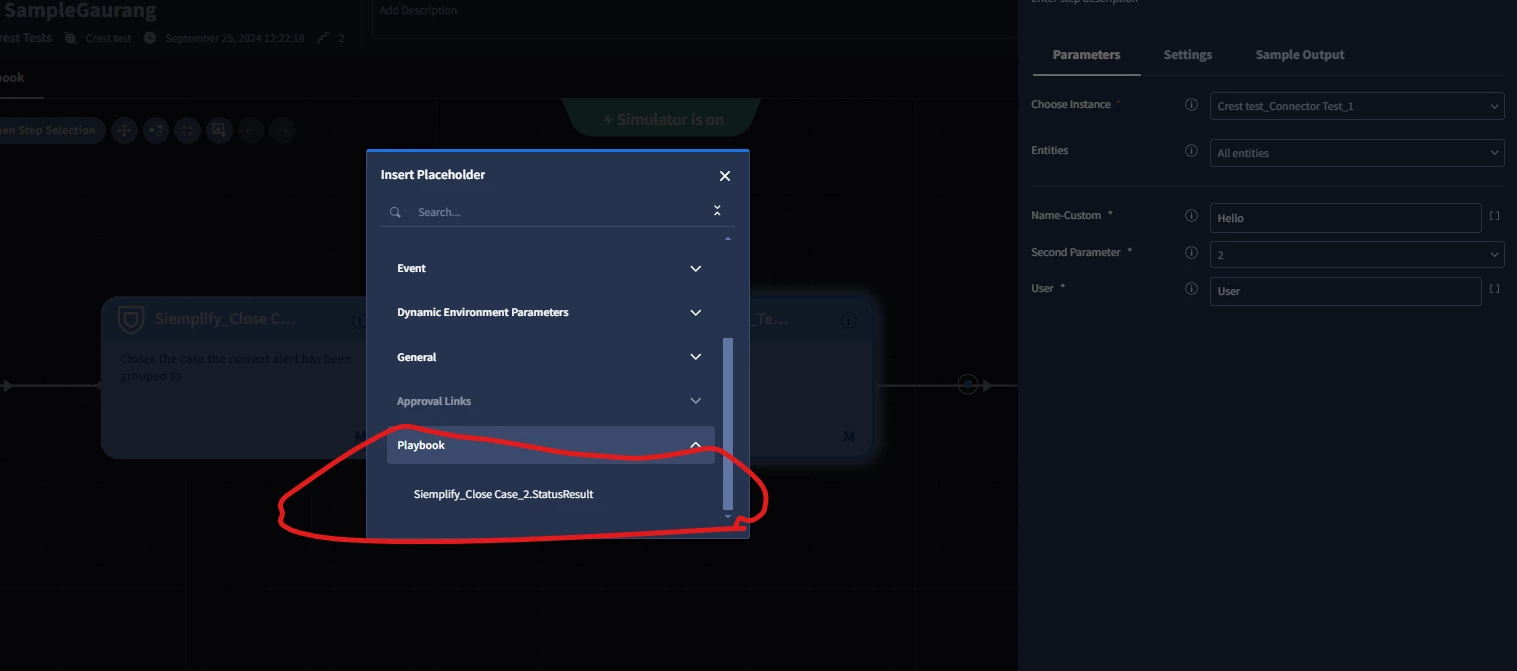
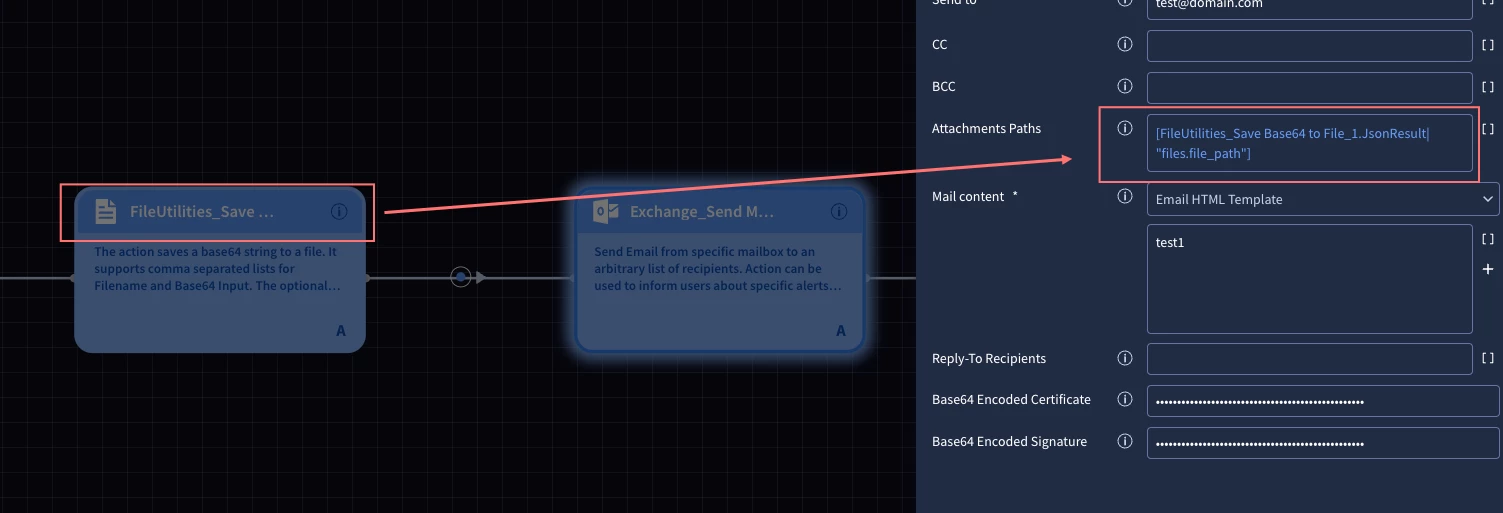
2. In flow you can use script results (json/text), selected parts of script results if this is JSON and also data from: cases, alerts, events, entity, environment and other parts of SOAR
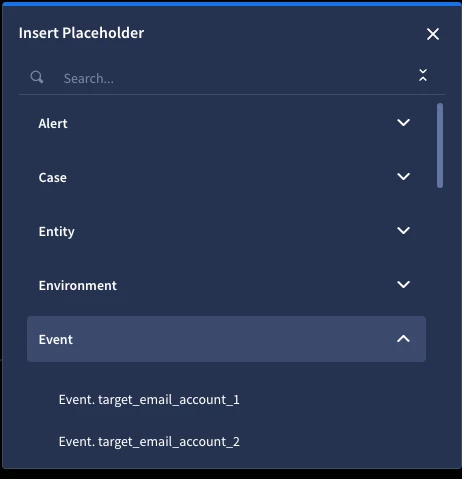
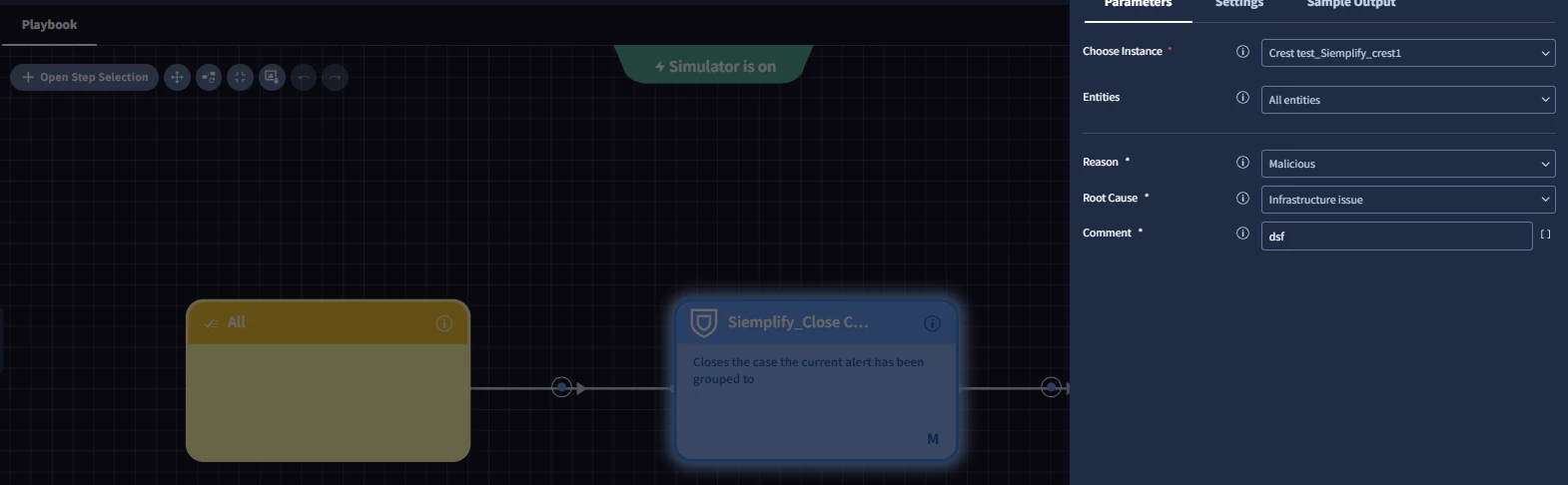
Adding some screenshots for a context:
---
1. Custom code execution is not possible with a playbook. It will require creating an integration and action and then being added to a playbook. So, it will be a Feature Request.
2. Capture inputs is possible with setting action to manually and assign a user to it, and then user should do inputs based on action you selected to let playbook continue.