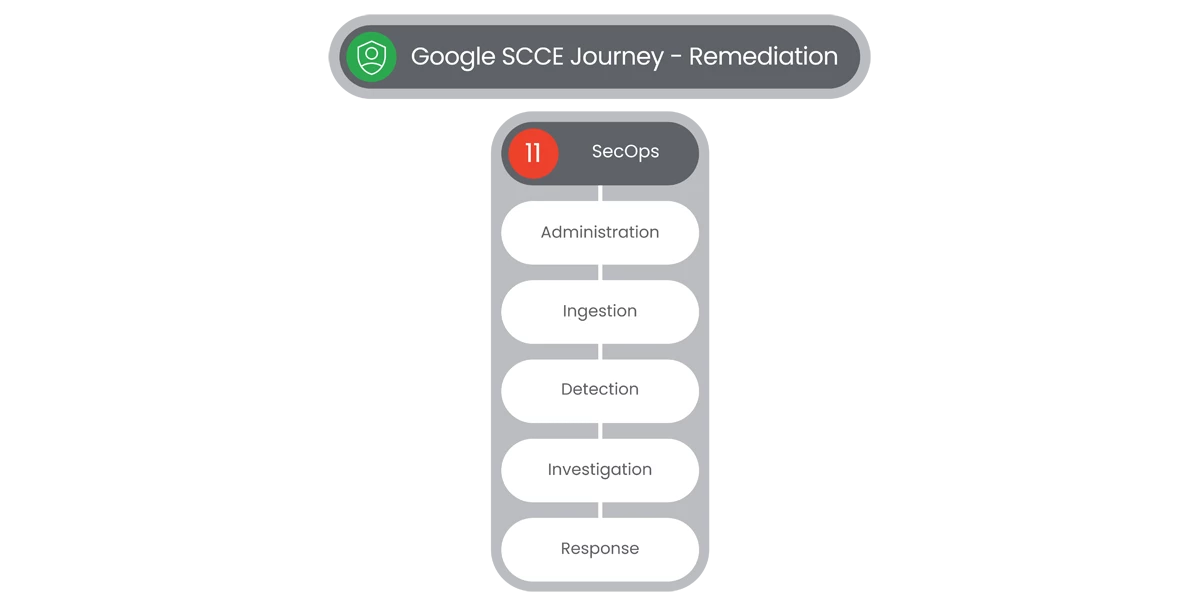
Table of Contents
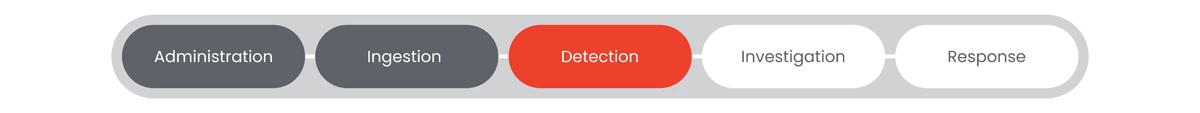
Detection
Threat Detection
Google SecOps Threat Detection feature allows for detection enrichment capabilities that enables security analysts and detection engineers to craft a detection on a basic pattern of event telemetry (an outbound network connection), creating numerous detections for their analysts to triage. The analysts attempt to stitch together an understanding of what happened to trigger the alert and how significant the threat is.
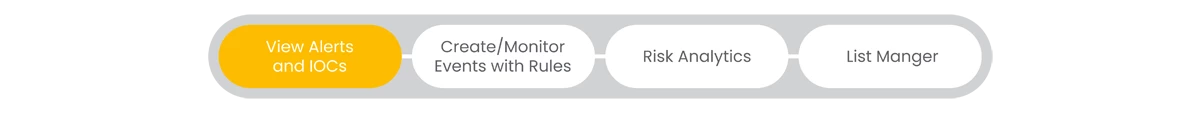
View Alerts and IOCs
Google SecOps features an Alerts and IOCs page, that displays all the alerts and indicators of compromise (IOC) currently impacting your enterprise. This provides multiple tools that enable you to filter and view your alerts and IOCs.
Steps
- Users will navigate to the left-side Navigation Bar and then select Detection, which will display a dropdown menu.
- Select Alerts & IOCs to display the Alerts & IOCs page.
- Users will see two tabs:
- Alerts
- IOC Matches
- Users will have options in the popout page, under the Alerts tab consisting of:
- Manage Columns
- Filter
- Status
- Clear All
- Search Bar
- Refresh Time
- Showing (Date Range)
- Refresh
- Alerts List Options

- Under the IOC Matches tab, users will see a Procedural Filtering section consisting of:
- IOC Categories
- IOC Confidence Score
- IOC Feed
- IOC/ Alert Severity
- At the top of the IOCs list popout, users will see Filter
 options consisting of:
options consisting of: - IOC Matches
- Fetch Limit
- Download as CSV
- Refresh Time
- Date Range
- In the IOCs popout section, users will see a list of IOCs with multiple columns:
- IOC
- Categories
- Sources
- Assets
- Confidence
- Severity
- IOC Ingest TIme
- First Seen
- Last Seen
Relevant Documentation Links
Create/ Monitor Events w/ Rules
Google SecOps features Rules feature, that are the backbone of ensuring data is actionable and aligned to your unique policies within Google SecOps. Rules allow your SecOps team to tailor information and alerting to the unique needs of your organization.
Steps
- Users will navigate to the left-side Navigation Bar and then select Detection, which will display a dropdown menu.
- Select Rules & Detections in the dropdown to display the Rules & Detections page.
- The Rules & Detections page will display four tabs consisting of the following features:
- Rules Dashboard
- Rules Editor
- Curtated Detections
- Exclusions
- In the Rules Dashboard, users will see the following features at the top of the page:
- Search Rules
- Data Freshness
- Last Refreshed Time
- Below in the Rules Dashboard users will be able to see a Rules List consisting of the Rules Search results.
- The Rules Dashboard results list consists of the following columns:
- Number of Detections Found Today
- Rule Name
- Detections Per Day
- Last Detection
- Author
- Severity
- Alerting
- Retrohunt
- Rule Type
- Run Frequency
- Live Status
- The Rules Editor page will display the capability to:
- Create New Rule

- Filter

- Reference List
Note: Create New Rule is disabled in Google SCCE versions of SecOps.
- Create New Rule
- Users will have the capability to select from a Curated Detection list under the Curated Detections tab.
- At the top of the page, users will see a display of the highlighted Rules, consisting of:
- Enabled Rule Sets
- Most Active Rules
- Most Active Rule Sets
- Users will also be able to see in the main section of Curated Detections:
- Rules Sets
- Rules Dashboard
- In the Rule Sets section, users will see displayed, a list of Rule Sets, with the following columns:
- Name
- Last Updated
- Enabled Rules
- Alerting
- Capacity
- MITRE Tactics
- MITRE Techniques
- When a Rule Set is selected, user will see a display page of the Rule’s Settings and Sources.
- In the Exclusions page, users will see a display of Exclusions, with the following columns:
- Exclusion Name
- Applied To
- Activity
- Created On
- Last Updated
- Status
- Users can create an Exclusion by selecting Create Exclusion.
- In the Create An Exclusion popup, users can filter out Detections that meet specific criteria, under the following entry fields:
- Exclusion Name
- Rule Set or Rule
- UDM Field
- Operator
- Values
- Add Conditional Statement
- Users will have an option to test the Exclusion Rule by selecting Run Test.

- To add the Exclusion Rule, users will select Add Rule Exclusion.

Relevant Documentation Links
List Manager
Google SecOps List Manager is a tool that allows users to manage reference lists and add custom lists. Users can add scopes to reference lists, open reference lists associated with rule sets, and add items to them.
Steps
- Users will navigate to the left-side Navigation Bar and then select Detection, which will display a dropdown menu.
- Select List in the dropdown to display the List Manager page.
- The List Manager page will display a popout of the Lists available to the user, along with the List Details and who the List is Referenced By.
- Users will be able to Create a List by selecting Create in the List Manger.

Relevant Documentation Links
Next Step: Security Command Center Enterprise: Step 4.1.4 - Remediation | Google SecOps | Investigation
Previous Step: Security Command Center Enterprise: Step 4.1.2 - Remediation | Google SecOps | Ingestion